Splunk | RS
How is the Splunk integration useful?
IT administrators using Splunk can integrate BeyondTrust Remote Support (RS) to strengthen access control, identify and prioritize threats seamlessly in real time, and remediate incidents proactively.
Through the integration, security events generated by Remote Support and appliance interfaces and any clients that generate syslog messages (such as the representative console) are captured through BeyondTrust Remote Support's rich logging capability. This integration securely populates this data into Splunk's platform, and reports are provided for security review.
Prerequisites
Software versions
Using this integration requires the following software and versions:
- A currently supported version of BeyondTrust Remote Support. To confirm your version is supported, contact Support or refer to the BeyondTrust End of Life Policy.
- Splunk On-Premises or Cloud: 6.3.0 or newer.
Network considerations
The following network communication channels must be open for the integration to work properly:
| Outbound From | Inbound To | TCP Port # | Purpose |
|---|---|---|---|
| Splunk Server | BeyondTrust Appliance B Series | 443 | Session event data pulled from the Reporting API |
| BeyondTrust Appliance B Series | Splunk Server | 6514 | Syslog event information from the B Series Appliance |
Configure Remote Support
The Splunk integration supports consumption of syslog output directly from the B Series Appliance.
To enable this, follow the steps below to create the syslog feed, verify the API is enabled, and create an OAuth API account.
Create the syslog feed
-
Sign into your your Remote Support appliance (B Series Appliance for Remote Support On-Premises users, or the virtual appliance for Remote Support Cloud users).
-
From the top menu, click Security > Appliance Administration.
The Syslog page displays.
The image below is modified to show only the relevant Syslog section on the page.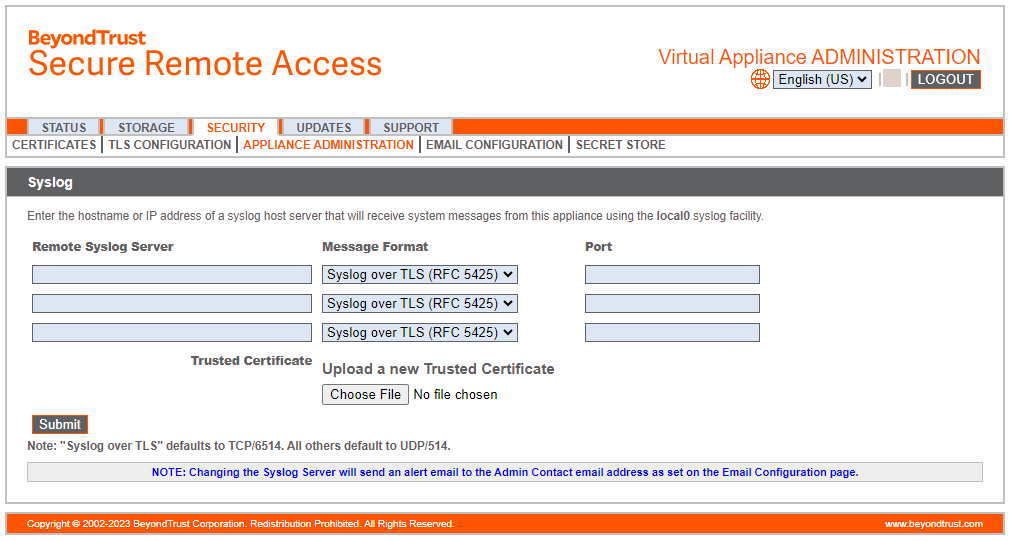
-
In the Syslog section, enter the hostname or IP address for your Remote Syslog Server.
-
Select your preferred message format.
Important informationWe highly recommend Syslog over TLS.
-
For Syslog over TLS message formats:
- Obtain the trusted certificate configured for your Splunk listener/input .
- Click Choose File.
- Navigate to your trusted certificate.
- Click Open.
The file uploads to the site.Because Splunk Cloud does not natively support inputs, you must use a forwarder (such as Splunk's Universal Forwarder.
Refer to Splunk documentation and support for guidance on configuring a certificate for the input or forwarder.
-
Click Submit.
The syslog feed is created.
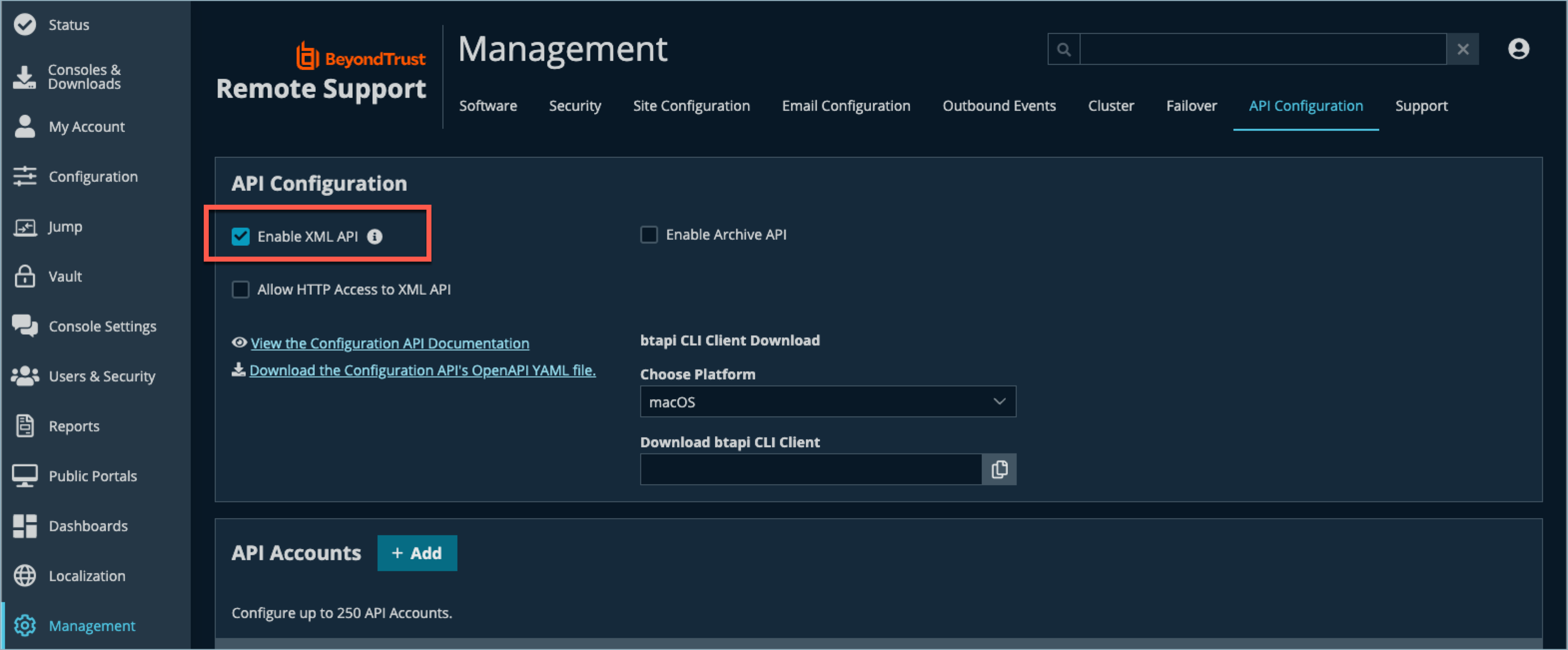
Verify the API Is enabled
This integration requires the BeyondTrust XML API to be enabled. This feature is used by the Splunk app to communicate with the BeyondTrust APIs.
-
Sign into Remote Support for Admins.
-
From the left menu, click Management.
The Management page displays. -
From the top menu, click API Configuration.
The API Configuration page displays. -
Verify that Enable XML API is checked.
Create an OAuth API account
The Splunk API account is used from within Splunk to make Remote Support Command API calls to Remote Support.
-
Sign into Remote Support for Admins.
-
From the left menu, click Management.
The Management page displays. -
From the top menu, click API Configuration.
The API Configuration page displays. -
In the API Account section, click Add.
The Add API Configuration page displays. -
Check Enabled.
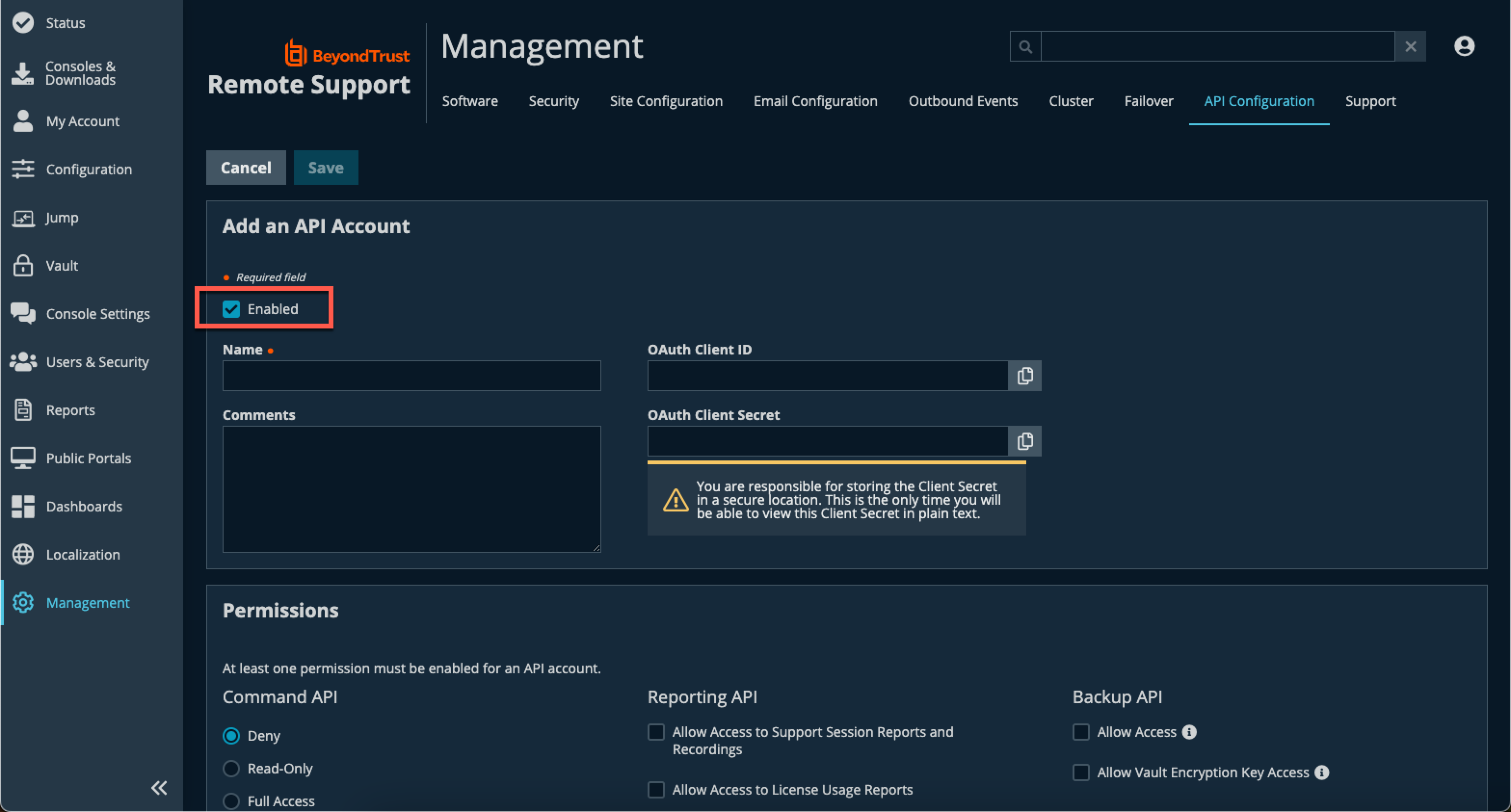
-
Enter a name for the account.
OAuth Client ID and OAuth Client Secret is used during the OAuth configuration step in Splunk.
-
Under Permissions, select the following:
- Reporting API: Allow Access to Support Session Reports and Recordings and Allow Access to Presentation Session Reports and Recordings
-
Click Save at the top of the page.
The OAuth API account is created.
Configure Splunk
The integration application is available in the Splunkbase. You must log in to your Splunk account to download the application.
Once the new application is installed, follow these steps in the app to configure it:
- In the list of Splunk Apps, click the new BeyondTrust Remote Support option.
- On the BeyondTrust Remote Support Inputs page, click Create New Input.
- Enter the required input information:
- Name: Desired unique input name.
- Interval: Desired polling interval. A short polling interval can result in poor performance. At least 60 seconds is recommended.
- Index: Must be beyondtrust_rs. Create this index if it does not already exist.
- RS Site hostname: Your Remote Support hostname. Do not include the protocol (https://) or other URL components. This value must be the hostname only. For example, support.example.com.
- Client ID: Your previously configured Client ID.
- Client Secret: Your previously configured Client Secret.
- Click Add.
Troubleshooting
Selected timeframe is incorrect
Ensure the selected timeframe is correct and verify that sessions have ended or administrative actions are taken within that timeframe.
To do this, click Show Filters and make sure that the timeframe you've chosen is one in which data should exist.
Input interval is not completed
Ensure that the input interval has run since the data you're expecting to see was generated. This only applies to session data / events.
For example, if you ran a test session that ended one minute ago but the input is set to run every two minutes (120 seconds), it's possible that the app simply hasn't queried for new data since your test session ended.
Verify index data that uses queries
Check the indexed data behind the queries. To do this, hover with your mouse over any dashboard section, click Open in Search. This lets you see the actual query and events that are fed into a section. You can expand your search by expanding the timeframe, editing the query to remove some of the filters, or both.
Administrative actions are missing
If you seem to be missing events that represent administrative actions, verify your Syslog configuration on the appliance as well as the corresponding input in Splunk.
An administrative action for the purpose of this question is either a login or logout process or any time a configuration change that takes place on the BeyondTrust instance.
Events are missing within a session
If you seem to be missing events that represent actions within a session and have verified the things that apply to this source of data, it may be helpful to check the Splunk App's logs.
- On a Splunk Enterprise site where you have access to the file system, you can find the actual log file under the Splunk install directory or a path similar to:
<path_to_splunk_install>\var\log\splunk\beyondtrust_pra_integration_beyondtrust_pra_reporting_api_session_events.log
- On a Splunk Cloud site or if you don't have access to the file system for a Splunk Enterprise deployment, application logs should be indexed and searchable via the standard Search and Reporting interface in Splunk.
To do this, navigate to that app, select an appropriate timeframe, and enter the following basic search query:
index="_internal" sourcetype="beyondtrustpraintegration:log"
You should have the app's log level set to DEBUG to get the best results. To set the level, go to the Configuration tab on the app.
Troubleshooting
Selected timeframe is incorrect
Ensure the selected timeframe is correct and verify that sessions have ended or administrative actions are taken within that timeframe.
To do this, click Show Filters and make sure that the timeframe you've chosen is one in which data should exist.
Input interval is not completed
Ensure that the input interval has run since the data you're expecting to see was generated. This only applies to session data / events.
For example, if you ran a test session that ended one minute ago but the input is set to run every two minutes (120 seconds), it's possible that the app simply hasn't queried for new data since your test session ended.
Verify index data that uses queries
Check the indexed data behind the queries. To do this, hover with your mouse over any dashboard section, click Open in Search. This lets you see the actual query and events that are fed into a section. You can expand your search by expanding the timeframe, editing the query to remove some of the filters, or both.
Administrative actions are missing
If you seem to be missing events that represent administrative actions, verify your Syslog configuration on the appliance as well as the corresponding input in Splunk.
An administrative action for the purpose of this question is either a login or logout process or any time a configuration change that takes place on the BeyondTrust instance.
Events are missing within a session
If you seem to be missing events that represent actions within a session and have verified the things that apply to this source of data, it may be helpful to check the Splunk App's logs.
- On a Splunk Enterprise site where you have access to the file system, you can find the actual log file under the Splunk install directory or a path similar to:
<path_to_splunk_install>\var\log\splunk\beyondtrust_pra_integration_beyondtrust_pra_reporting_api_session_events.log
- On a Splunk Cloud site or if you don't have access to the file system for a Splunk Enterprise deployment, application logs should be indexed and searchable via the standard Search and Reporting interface in Splunk.
To do this, navigate to that app, select an appropriate timeframe, and enter the following basic search query:
index="_internal" sourcetype="beyondtrustpraintegration:log"
You should have the app's log level set to DEBUG to get the best results. To set the level, go to the Configuration tab on the app.
Updated 9 days ago
