February release notes draft
✨ Enhancements
See indirect access paths across AWS, Active Directory, and Google Workspace
Permissions views now display indirect access across AWS, Active Directory, and Google Workspace, including access granted through nested groups, intermediary roles, or other inherited relationships. This ensures the permissions graph, entitlement views, and access reviews reflect effective access, not just direct assignments, giving admins a more accurate picture of who can access what across these integrations.
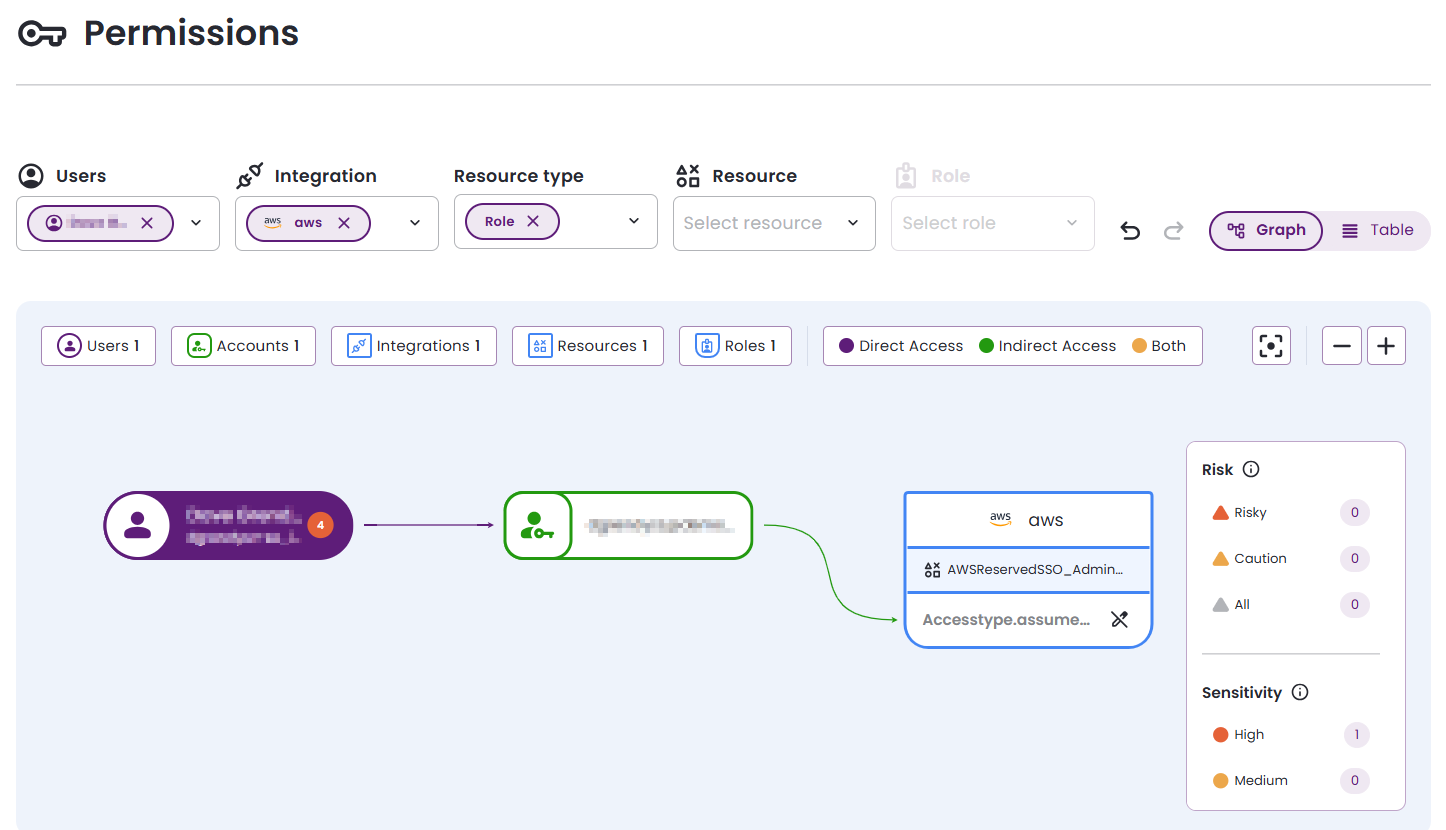
For information about the permissions graph, see The permissions graph.
Experience consistent access controls across Entitle workflows
Access controls are now handled more consistently across approval workflows, the permissions graph, org settings, users, tasks, and audit logs. This makes it easier to understand and control who can access what throughout Entitle, with the same permission types interpreted and displayed consistently across screens.
For more information, see:
Get clearer, threaded Slack notifications for approval workflows
Slack approval notifications are now consolidated into a single thread per access request, making it easier to follow the full decision history. Channels acting as approvers or notifiers receive clearer updates that show who approved a request, when it was approved, and how it progressed, improving visibility and auditability directly within Slack.
For more information, see Approval workflows.
Track Okta admin role changes through webhook events
The Okta integration webhook now supports additional events related to admin role changes. These include assignment and removal of predefined admin roles, as well as creation and deletion of custom admin role assignments through resource sets. This ensures changes to Okta administrative privileges are captured and processed more completely within Entitle.
For more information, see Okta webhooks.
Search and filter more efficiently across Bulk Actions and Birthright policies
Bulk Actions now supports search across integrations, resources, roles, workflows, owners, maintainers, IdP groups, and users, making it easier to target the correct items before applying updates. The Birthright Policies page also includes search and filtering, helping admins quickly locate and manage policies in larger or more complex environments.
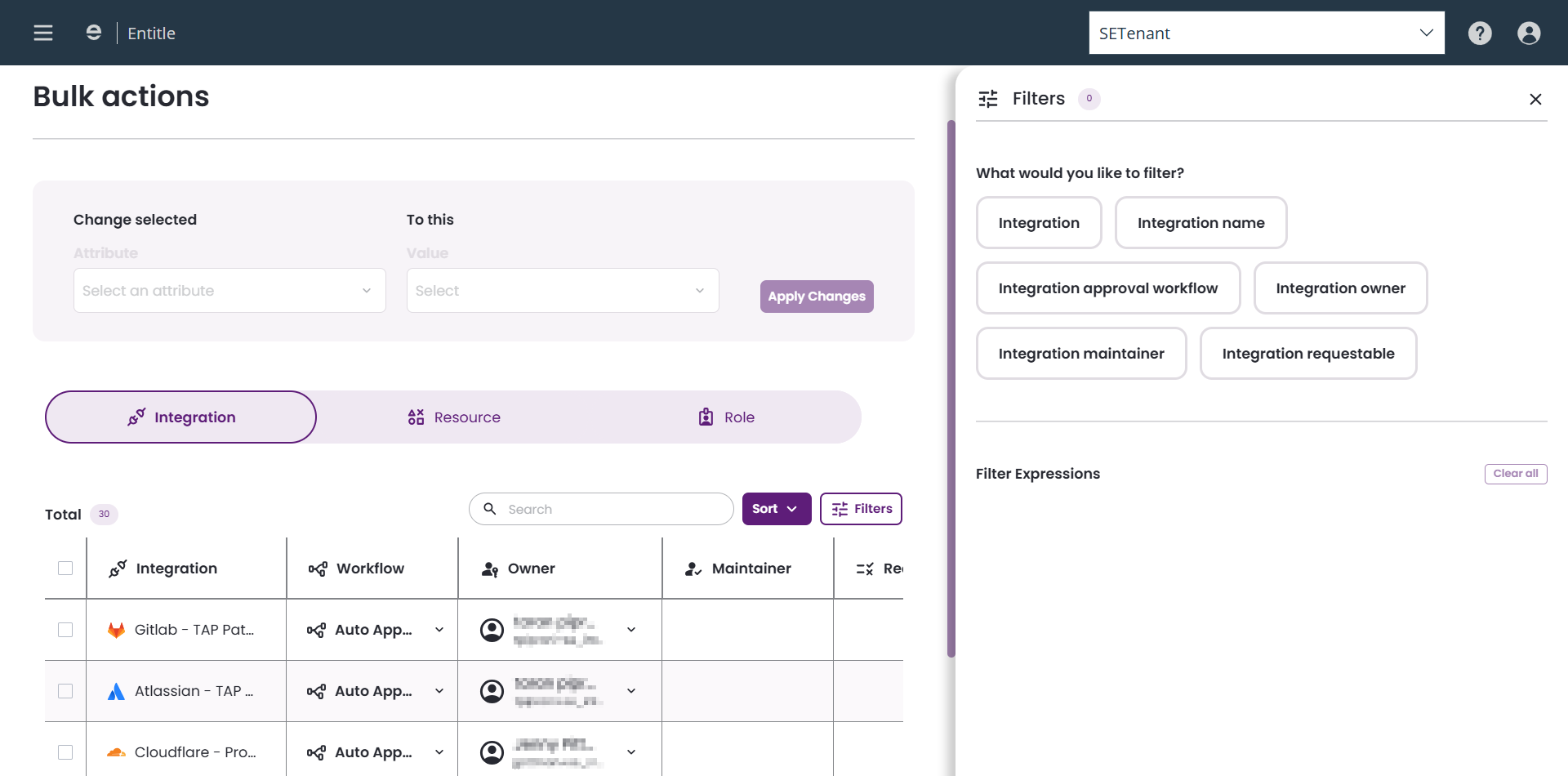
For more information, see Birthright policies.
Connect Jamf to Entitle without disabling SSO
The Jamf integration now supports environments where SSO is enabled, using modern authentication flows instead of relying solely on basic authentication. Customers can connect Jamf to Entitle without disabling SSO, while maintaining their existing identity and security controls.
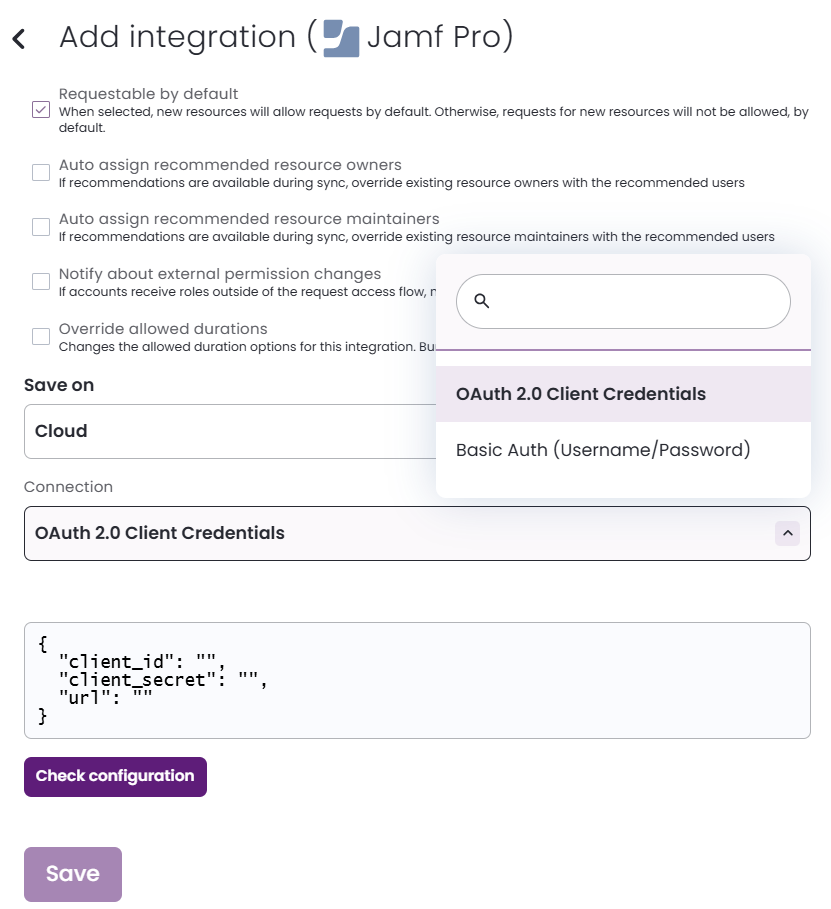
For more information, see Jamf Pro.
See only managed resources and roles when configuring virtual applications
The virtual integration resource and role picker now displays only managed resources and roles. By excluding unmanaged items and integrations without managed resources, the selection experience is cleaner and reduces the risk of misconfiguration.
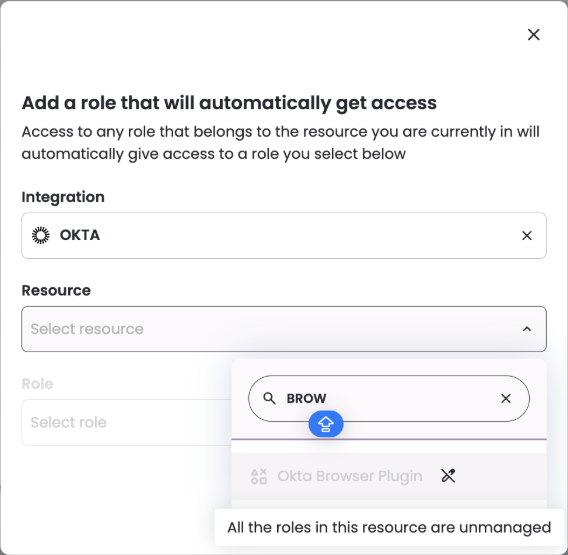
For more information, see Integrations, resources, and roles.
See improved accuracy and usability in the JIT request analysis report
The JIT request analysis report has been enhanced to improve data accuracy and usability, and to better align with how Entitle represents user entitlements and access relationships. The report now more reliably reflects current roles, resources, and effective access, giving stakeholders greater confidence when using it for operational monitoring and compliance reviews.
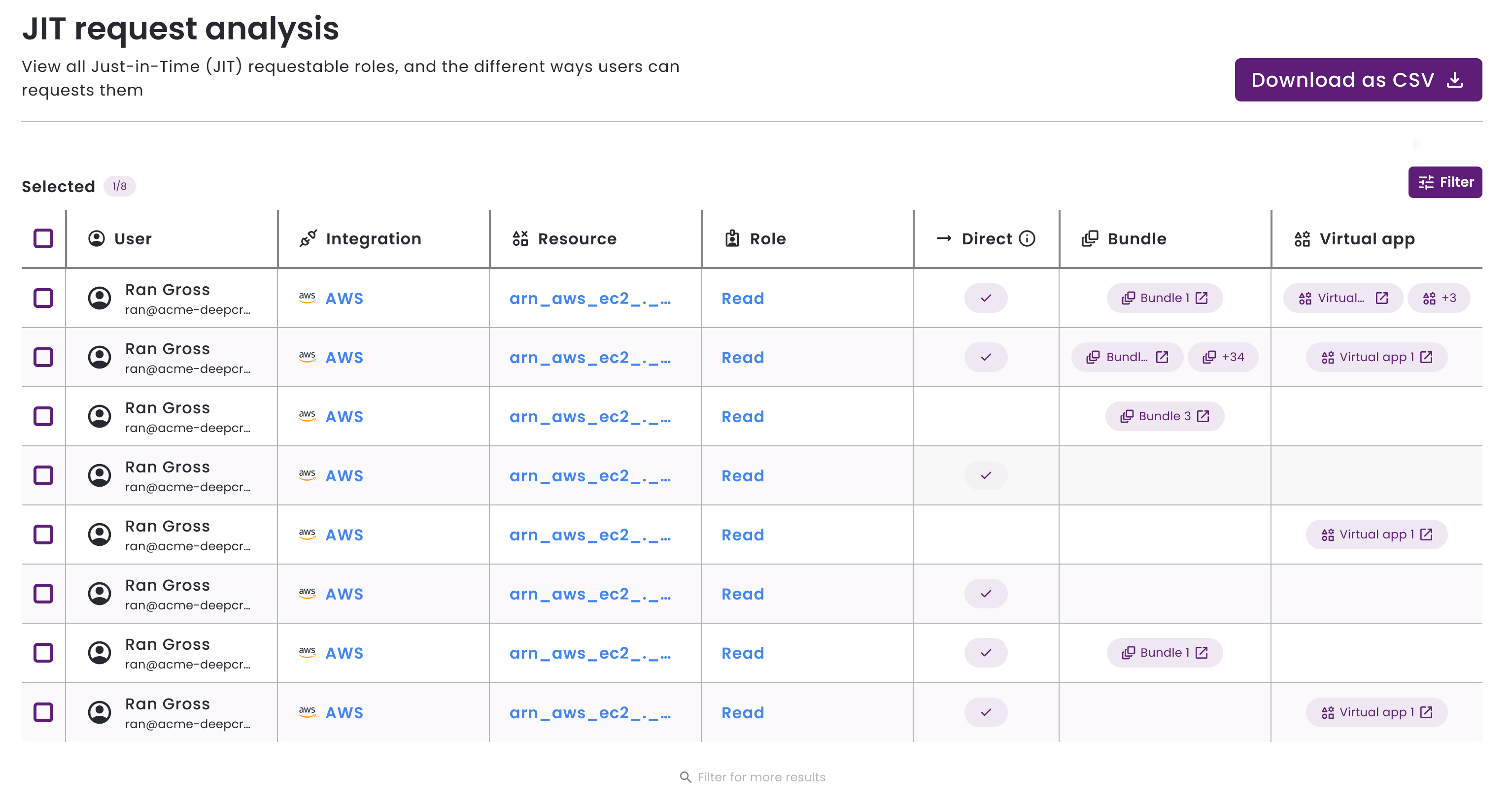
For information about this report, see View JIT request analysis.
Discover available Entitle applications programmatically
Terraform users can now retrieve the list of Entitle applications directly through the provider, eliminating the need for hard-coded values when defining integrations. This allows infrastructure teams to discover applications programmatically and incorporate them into automation workflows with greater confidence.
For more information about Terraform, see Terraform Cloud.
Manage virtual applications more reliably with Terraform
Infrastructure supporting a virtual application is now managed through Terraform, enabling consistent and repeatable provisioning across environments. Managing these resources as infrastructure as code reduces configuration drift and makes future updates safer and easier to audit.
For more information about Terraform, see Terraform Cloud.
See consistent bundles, policies, and tags behavior across screens
Bundles, policies, and tags now behave consistently across configuration screens. These updates make entitlement configuration more predictable and easier to manage, especially in large or complex tenants.
Experience more reliable and understandable handling of complex access scenarios
Several enhancements were made to improve how Entitle models and processes complex access scenarios across integrations. These updates increase the reliability of permission handling and improve how effective access is calculated and displayed, reducing the need for manual corrections and making access behavior easier to understand.
📑 Documentation
Get clearer guidance when using Entitle public APIs
Entitle’s public API documentation has been expanded to provide clearer guidance on required and optional parameters, expected value formats, and edge cases. The updates also clarify how to obtain referenced IDs and how virtual or manual applications behave in different scenarios, making integrations smoother for API and Terraform users.
To see the updated documentation, see the API reference.
Updated 3 months ago
