Group policies | PRA Pathfinder
What are Group policies?
Group policies define permissions and settings for groups of users, enabling administrators to standardize and streamline access control.
How are Group policies useful?
Group policies help ensure consistency in user permissions, simplify administrative tasks, and support secure and efficient management of user groups.
How do I access the Group Policies page?
- Sign into app.beyondtrust.io.
The BeyondTrust Home page displays. - From the main menu, click Privileged Remote Access > Users & Security.
The User & Security page opens and the Users tab displays by default. - Click the Group Policies tab.
The Group Policies tab displays.
The Group Policies page
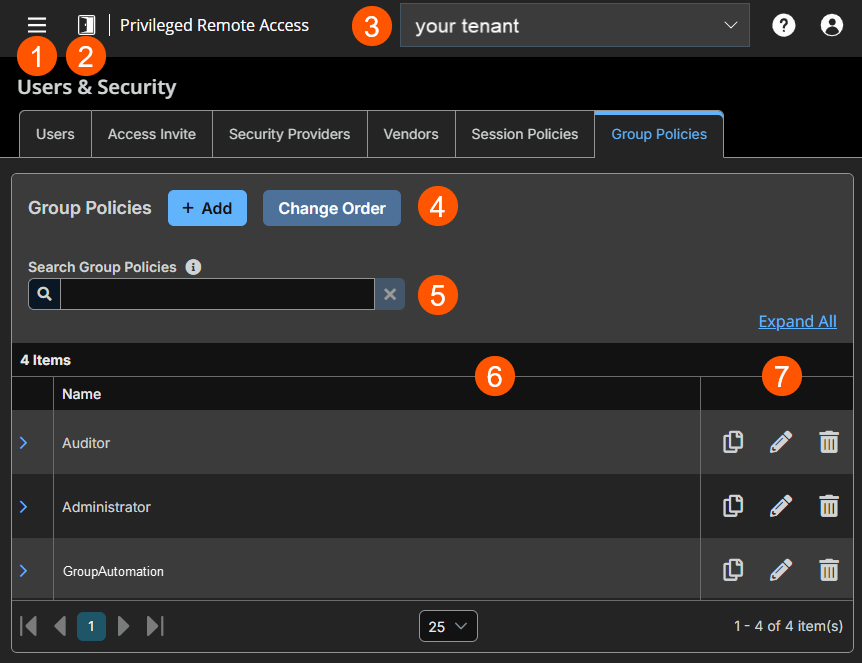
- Left menu: Easy access to all pages in Privilege Remote Access, including Status, Consoles & Downloads, My Account, Configuration, Asset Management, Vault, Console Settings, Users & Security, Reports, Management, and Appliance pages.
- Status: Opens the Status page.
- Header: Change your tenant site, manage your profile, and access documentation.
-
Add: Adds a new group policy and change order of policy priority.
-
Filter: Search for group policies using the Name field.
-
Group Policies columns: The list of Group Policies columns.
Group Policies columns
- Name: Unique name of the group policy.
-
Group Policies list options: Copy, edit or delete a group policy.
Add a new policy
- Sign into app.beyondtrust.io.
The BeyondTrust Home page displays. - From the main menu, click Privileged Remote Access > Users & Security.
The User & Security page opens and the Users tab displays by default. - Click the Group Policies tab.
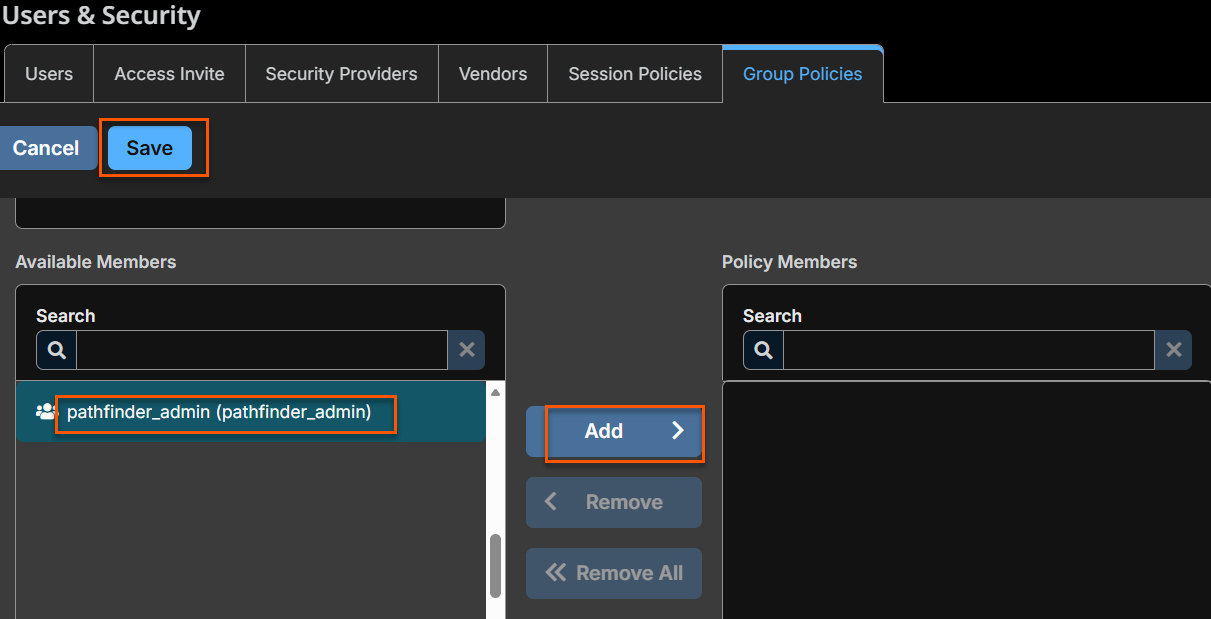
The Group Policies tab displays. - Click Add.
The Add New Policy page displays. - For Policy Name, enter a unique name for the policy.
- For the Available Members, select a member to assign and click Add to move them to the Policy Members list.
You can use the Search box to find existing members. You can select users from your local system or select users or entire groups from configured security providers. If an attempt to add a user from a configured security provider is invalid, the synchronization log error message appears here as well as in the log. - Select the various group policy settings. See Group Policy settings.
- Click Save.
Copy a policy
To expedite the creation of similar policies, you can copy a policy with identical settings. You can then edit this new policy to meet your specific requirements.
- Sign into app.beyondtrust.io.
The BeyondTrust Home page displays. - From the main menu, click Privileged Remote Access > Users & Security.
The User & Security page opens and the Users tab displays by default. - Click the Group Policies tab.
The Group Policies tab displays. - Find the group policy you want to duplicate, and click Copy
 .
. - The Add new policy page loads with the settings matching the original policy. Make any adjustments needed, then click Save.
Edit a policy
- Sign into app.beyondtrust.io.
The BeyondTrust Home page displays. - From the main menu, click Privileged Remote Access > Users & Security.
The User & Security page opens and the Users tab displays by default. - Click the Group Policies tab.
The Group Policies tab displays. - Find the group policy you want to edit, and click Edit
 .
. - The Edit policy page loads. Make any adjustments needed, then click Save.
If you edit the group policy that is the default for the local provider, or has local administrator users, and remove administrator permissions, a warning message appears. Ensure other users have administrator permissions before proceeding.
Delete a policy
- Sign into app.beyondtrust.io.
The BeyondTrust Home page displays. - From the main menu, click Privileged Remote Access > Users & Security.
The User & Security page opens and the Users tab displays by default. - Click the Group Policies tab.
The Group Policies tab displays. - Find the group policy you want to remove, and click Delete
 .
. - When prompted, click Yes.
Change order
Click the Change Order button to drag and drop group policies to set their priority. Click Save Order for prioritization changes to take effect. When multiple policies apply to a given user, the permissions take effect by starting at the top of the Group Policies list, and then moving down the list. If a permission conflicts with a permission applied by a group policy higher in the list, then the lower permission will overwrite the higher, unless the higher was set as Final. By changing the order, you are changing the priority of the group policy. In short, group policies that appear lower in the list have a higher functional priority than those that are higher.
Search group policies
To quickly find an existing policy in the list of Group Policies, enter the name, or part of the name. The list filters to all policies with a name containing the entered search term. The list remains filtered until the search term is removed, even if the user goes to other pages or logs out. To remove the search term, click the X to the right of the search box.
Expand all / collapse all
To assist with searching and navigating the group policies, click the Expand All link above the grid to expand the details of all listed group policies. Click Collapse All to return to the unexpanded list of group policies.
Group Policy settings
Which settings should this group policy control?
When you create a new group policy, you must select the settings and membership(s) that are either defined in the policy or left available for configuration for individual users. The list of settings is the following:
- Account Settings: Controls settings such as Two Factor Authentication, Account Expiration and Account enablement.
- General Permissions: Controls a variety of Administration and Reporting settings.
- Access Permissions: Settings that allow access to Endpoints.
- Sessions Permissions: Settings that control Session Policies.
- Availability Settings: Settings that determine a login schedule.
- Memberships: Settings that control the Add & Remove permissions for the following:
- Team membership
- Gateway membership
- Asset Group membership
- Vault Account and Account Group memberships
If a policy setting is defined, you are not able to modify that privilege for an individual user from their user account page.
If you have a policy that defines a permission and you do not want any policy to be able to replace that permission, then you must select that the permission cannot be overridden, and the policy must be a higher priority than other policies that additionally define that setting.
- Policy name: Enter a unique name that distinguishes this policy from others, usually based on the assigned permission level or the job function it supports.
- Available members: Users with access to your Privileged Remote Access site. Click Add > to move them to the Policy members list and apply this policy's settings to them. To remove access, select a member and click < Remove, or click << Remove All to clear the list.
Important informationIf a setting is Defined, it is controlled by this policy. You are not able to modify that privilege for an individual user from their user account page.
If it is not defined, it can be set individually.
If you have a policy that defines a permission and you do not want any policy to be able to override that permission, then you must set that permission as Final, and the policy must be a higher priority than other policies that additionally define that setting.
### Account settings
- Two Factor Authentication
- Log in with an authenticator app: Two factor authentication (2FA) uses an authenticator app to provide a time-based, one-time code to login to the administrative interface, as well as the access console.
- If Required is selected, the user is prompted to enroll and begin using 2FA at the next login.
- If Optional is selected, the user has the option to use 2FA, but it is not required.
- Log in with an authenticator app: Two factor authentication (2FA) uses an authenticator app to provide a time-based, one-time code to login to the administrative interface, as well as the access console.
- Account Expiration:
- Account Never Expires: When checked, the account never expires. When not checked, an account expiration date must be set.
- Account expiration date: Causes the account to expire after a set date.
- Account Enablement
- Account disabled: Allows you to disable the account so the user cannot log in. Disabling does NOT delete the account.
- Comments: Add comments to help identify the purpose of this object.
General permissions
- Administration
- Administrative privileges
- Administrator: Grants the user full administrative rights.
- Vault Administrative Privileges
- Allowed to administer Vault: Enables the user access to the Vault.
- Password Setting
- Allowed to Set Passwords and Reset MFA: Allows a user to set passwords for non-administrative users and to unlock non-administrative user accounts that were locked due to too many consecutive login attempts.
- Gateway editing
- Allowed to Edit Gateways: Enables the user to create or edit Gateways. This option does not affect the user's ability to access remote computers via Gateway, which is configured per Gateway or group policy.
- Team Editing
- Allowed to Edit Teams: Enables the user to create or edit teams.
- Asset Group Editing
- Allowed to Edit Asset Groups: Enables the user to create or edit Asset Groups.
- Canned Script Editing
- Allowed to Edit Canned Scripts: Enables the user to create or edit canned scripts for use in screen sharing or shell sessions.
- Custom Link Editing
- Allowed to Edit Custom Links: Enables the user to create or edit custom links.
- Administrative privileges
- Reporting
- Session and Team Report Access
- Allowed to view access session reports: Enables the user to run reports on access session activity, viewing only sessions for which they were the primary session owner, only sessions for endpoints belonging to an Asset Group of which the user is a member, or all sessions.
- Allowed to view access session recordings: Enables the user to view video recordings of screen sharing sessions and shell sessions.
- Vault Report Access
- Allowed to view Vault reports: Enables the user to view his or her own vault events or all Vault events.
- Syslog Report Access
- Allowed to view syslog reports: Enables the user to download a ZIP file containing all syslog files available on the appliance. Admins are automatically permissioned to access this report. Non-admin users must request access to view this report.
- Session and Team Report Access
Access permissions
- Allowed to access endpoints: Enables the user to use the access console in order to run sessions. If endpoint access is enabled, options pertaining to endpoint access will also be available.
- Session management
- Allowed to share sessions with teams which they do not belong to: Enables the user to invite a less limited set of user to share sessions, not only their team members. Combined with the extended availability permission, this permission expands session sharing capabilities.
- Allowed to invite external users: Enables the user to invite third-party users to participate in a session, one time only.
- Remove User from session after inactivity: Sets the time interval to remove a user from a session after inactivity. Values range from No Timeout to 24 hours.
- Allowed to enable extended availability mode: Enables the user to receive email invitations from other users requesting to share a session even when they are not logged into the access console.
- Allowed to edit the external key: Enables the user to modify the external key from the session info pane of a session within the access console.
- Allowed to edit the external key: Enables the user to modify the external key from the session info pane of a session within the access console.
- User to user screen sharing
- Allowed to show screen to other users: Enables the user to share their screen with another user without the receiving user having to join a session. This option is available even if the user is not in a session.
- Allowed to give control when showing screen to other users: Enables the user sharing their screen to give keyboard and mouse control to the user viewing their screen.
- Jump Technology
- Allowed Asset methods: Enables the user to connect to computers using the following:
- Jump Clients
- Local Jump (Windows only)
- Remote Jump
- Remove VNC
- Web Jump
- Remote RDP
- Shell
- Database Connection
- Asset Roles: An Asset Role is a predefined set of permissions regarding Asset management and usage. For each option, click Show to open the Asset Role in a new tab.
- The Default role is used only when Use User's Default is set for that user in an Asset Group.
- The Personal role applies only to Assets pinned to the user's personal list of Assets.
- The Teams role applies to Assets pinned to the personal list of Assets of a team member of a lower role. For example, a team manager can view team leads' and team members' personal Assets, and a team lead can view team members' personal Assets.
- The System role applies to all other Assets in the system. For most users, this should be set to No Access. If set to any other option, the user is added to Asset Groups to which they would not normally be assigned, and in the access console, they can see non-team members' personal lists of Assets.
- The Endpoint automation role sets how a user can use endpoint automation.
- Not allowed prevents them from seeing the Asset Management > Endpoint Automation tab altogether.
- A User can create new automation jobs with these restrictions:
- They are able to choose any existing Script Template but cannot edit the Script Template, Script Command, nor select or change the template accompanying Resources.
- The Script Template, Script Command, Operating System, and Resources fields are unavailable.
- They can run scripts only on Assets where their Asset Role includes the Start Sessions permission (set on the Asset Management > Assets Role page).
- An Administrator has full access and ability to create Jobs, Scripts Templates, and Resources.
For more information, see Asset Roles and Endpoint Automation.
- External tools
- Enable static port and username for external tool sessions: This option accepts two values:
- Enable: Ensures that the port and username generated for a user starting a session with an Asset using external tools are preserved from session to session.
- Disable: A new port number and username are randomly generated for that user every time they start a new session with each Asset.
- Enable static port and username for external tool sessions: This option accepts two values:
- Allowed Asset methods: Enables the user to connect to computers using the following:
Session permissions
- Session policy: Set the prompting and permission rules that should apply to this user's sessions. Choose an existing session policy or define custom permissions for this user. If Not Defined, the global default policy will be used. These permissions may be overridden by a higher policy.
- Description: View the description of a pre-defined session permission policy.
- Allow Elevated Access to Shells, Tools and Special Actions on the Endpoint: If enabled, access to elevated functionality will be provided in the access console for this session without needing the explicit rights of a logged in user on the remote endpoint. This setting applies where allowed by the endpoint's platform.
- Allow Original Session Owner to Leave Sessions Running for Others: If enabled, this will leave the session running for others who have joined when the original owner leaves. Other users that have joined the session must already have been able to start a session with that Jump Client.
- Screen sharing
- Screen sharing rules: Select the user's and remote user's access to the remote system:
- If Not Defined, this option is set by the next lower priority policy. This setting may be overridden by a higher priority policy.
- Deny disables screen sharing.
- View Only allows the representative to view the screen.
- View and Control allows the user to view and take action on the system.
For more information, see control-the-remote-endpoint-with-screen-sharing.
- Clipboard synchronization direction: Available only if View and Control is selected above. Select how clipboard content flows between users and endpoints. The options are:
- Not allowed: The user is not allowed to use the clipboard, no clipboard icons display in the access console, and cut and paste commands do not work.
- Allowed from Rep to Customer: The user can push clipboard content to the endpoint but cannot paste from the endpoint's clipboard. Only the Send clipboard icon displays in the access console.
- Allowed in Both Directions: Clipboard content can flow both ways. Both Push and Get clipboard icons display in the access console.
For more information, see Screen sharing tools.
- Allowed endpoint restrictions: Available only if View and Control is selected above. Sets the option for the user to suspend the remote system's mouse and keyboard input. The user may also prevent the remote desktop from being displayed.
- None does not set any restrictions on the remote system.
- Display, Mouse, and Keyboard disables these inputs.
If this is selected, a check box is available to Automatically request a privacy screen on session start. Privacy screen is applicable only for sessions started from a Jump Client, a Remote Asset, or a Local Asset. We recommend using privacy screen for unattended sessions. The remote system must support privacy screen.For more information about the privacy screen, see Screen sharing options.
- Application sharing restrictions: This option limits access to specified applications on the remote system with either. There are three values:
- None
- Allow only the listed executables: Allows you to specify executables to allow as appropriate to your objectives.
- Deny only the listed executables: Allows you to specify executables to deny as appropriate to your objectives.
- If Allow or Deny is selected, you see the option to Add new executables to the allow or deny list. When you add executables, you have two choices:
- Enter file names or SHA-256 hashes, one per line: Manually enter the executable file names or hashes you wish to allow or deny. Click Add Executable(s) when you are finished to add the chosen files to your configuration.
You may enter up to 25 files per dialog. If you need to add more, click Add Executable(s) and then reopen the dialog. - Browse for one or more files: Choose executable files to automatically derive their names or hashes. If you select files from your local platform and system in this manner, use caution to ensure that the files are indeed executable files. No browser level verification is performed.
Choose either Use file name or Use file hash (advanced) to have the browser derive the executable file names or hashes automatically.
Click Add Executable(s) when you are finished to add the chosen files to your configuration. You may enter up to 25 files per dialog. If you need to add more, click Add Executable(s) and then reopen the dialog.
If Allow or Deny is selected, you may also choose to allow or deny desktop access.
- Enter file names or SHA-256 hashes, one per line: Manually enter the executable file names or hashes you wish to allow or deny. Click Add Executable(s) when you are finished to add the chosen files to your configuration.
- Screen sharing rules: Select the user's and remote user's access to the remote system:
- Application sharing restrictions applies only to Windows operating systems.
- The option to add executables to the list is available only in modern browsers, not legacy browsers.
-
System Sound Sharing
-
System Sound Sharing Rules: Allows the user to hear the endpoint's system sound during screen sharing when supported by the client. It does not allow access to the endpoint's microphone. If Not Defined is enabled, this option is set by the next lower priority policy. This setting may be overridden by a higher priority policy.
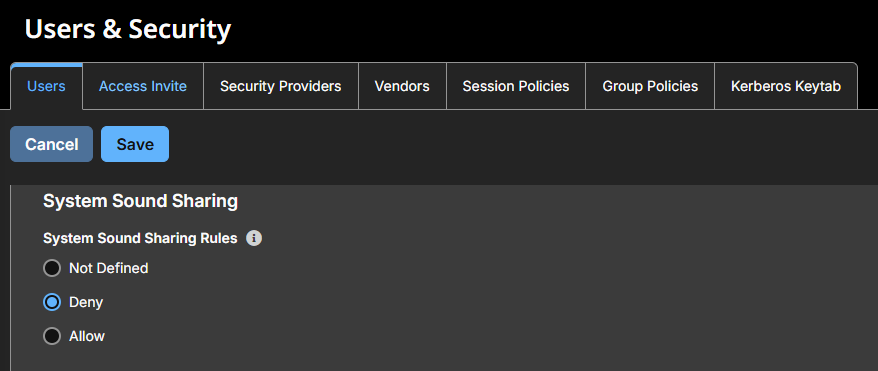
This feature only works if the representative has permissions for sound and if the site has the Peer To Peer option (located under Configuration > Options ) enabled. Enabling this option allows sound to be heard from the endpoint.
-
-
Annotations
- Annotation rules: Enables the user to use annotation tools to draw on the remote system's screen. If Not Defined is enabled, this option is set by the next lower priority policy. This setting may be overridden by a higher priority policy.
-
File transfer
- File Transfer Rules: Enables the user to upload files to the remote system, download files from the remote system, or both. If Not Defined is enabled, this option is set by the next lower priority policy. This setting may be overridden by a higher priority policy.
- Accessible paths on the endpoint's filesystem: Allow the user to transfer files to or from any directories on the remote system or only specified directories.
- Accessible paths on user's filesystem: Allow the user to transfer files to or from any directories on their local system or only specified directories.
For more information, see File transfer.
-
Shell
-
Shell Rules: Enables the user to issue commands on the remote computer through a virtual command line interface. If Not Defined is enabled, this option is set by the next lower priority policy. This setting may be overridden by a higher priority policy. Configure command filtering to prevent accidental use of commands that can be harmful to endpoint systems.
-
Allowed Executable Command Patterns: Available only if Shell rules is set to Allow. Enables the user to search for a regex pattern that matches a shell prompt. For filtering to work, the Recognized Shell Prompts section on the Asset Management > Asset page must be set and only filter commands in a Shell session.
- Shell access cannot be restricted for Shell sessions.
- For more information, see Command shell.
-
-
System information
- System Information Rules: Enables the user to see system information about the remote computer. If Not Defined is enabled, this option is set by the next lower priority policy. This setting may be overridden by a higher priority policy. You also have the option to set system information actions.
- Allowed to use system information actions: Enables the user to interact with processes and programs on the remote system without requiring screen sharing. Kill processes; start, stop, pause, resume, and restart services; and uninstall programs.
For more information, see System information.
-
Registry access
- Registry Access Rules: Enables the user to interact with the registry on a remote Windows system without requiring screen sharing. You have the ability to do the following actions:
- View, add, delete and edit keys
- Search and import/export keys
For more information, see Registry editor.
- Registry Access Rules: Enables the user to interact with the registry on a remote Windows system without requiring screen sharing. You have the ability to do the following actions:
-
Canned scripts
- Canned Script Rules: Enables the user to run canned scripts that have been created for their teams. If Not Defined is enabled, this option is set by the next lower priority policy. This setting may be overridden by a higher priority policy.
For more information about special actions and canned scripts, see Screen sharing tools and Command shell tools.
- Canned Script Rules: Enables the user to run canned scripts that have been created for their teams. If Not Defined is enabled, this option is set by the next lower priority policy. This setting may be overridden by a higher priority policy.
-
Session Termination Behavior
- When the access session ends, automatically: Controls what action to happen when session ends. The following options are:
- Not Defined
- Do Nothing
- Lock the computer
- Logout the user (Only works on Windows hosts).
- Allow users to override this setting per session: You can allow a user to override the session termination setting from the Summary tab in the console during a session.
For more information about closing a session and locking or logging out the end user, see Session tools.
- When the access session ends, automatically: Controls what action to happen when session ends. The following options are:
Availability settings
- Login schedule
- Restrict user login to the following schedule: Set a schedule to define when users can log into the access console. Set the time zone you want to use for this schedule, and then add one or more schedule entries. For each entry, click Add Schedule Entry to set the start day and time and the end day and time.
If, for instance, the time is set to start at 8 am and end at 5 pm, a user can log in at any time during this window but may continue to work past the set end time. They are not, however, allowed to log back in after 5 pm. - Force logout when the schedule does not permit login: If stricter access control is required, check this option. This forces the user to log out at the scheduled end time. In this case, the user receives recurring notifications beginning 15 minutes prior to being disconnected. When the user is logged out, any owned sessions follow the session fallback rules.
- Restrict user login to the following schedule: Set a schedule to define when users can log into the access console. Set the time zone you want to use for this schedule, and then add one or more schedule entries. For each entry, click Add Schedule Entry to set the start day and time and the end day and time.
Memberships
- Add team membership
- Add to teams: In the Team field, you can search for teams to which members of this group policy should belong. You can set the role as Team Member, Team Lead, or Team Manager. These roles play a significant part in the Dashboard feature of the access console. Once you have selected a team and team role, click Add.
The added teams are shown in a table. You can edit the role of members, click the pencil. To delete the team from the list, click the trash can.
- Add to teams: In the Team field, you can search for teams to which members of this group policy should belong. You can set the role as Team Member, Team Lead, or Team Manager. These roles play a significant part in the Dashboard feature of the access console. Once you have selected a team and team role, click Add.
- Remove Team Membership: When you select Remove Team Membership, the Remove From Teams section displays. This setting allows you to search for teams from which members of this group policy should be removed. From the result, you select the team, and then click Add. Removed teams are shown in a table. You can delete a team from the list.
- Add Gateway Memberships: When you select Add Gateway Membership, the Add to Gateway section displays. From Gateway, you search for Gateways in which members of this group policy should be allowed to access. From the result, click Add. The added Gateways are shown in a table. Click the trash can to delete a Gateway from the list.
- Remove Gateway Memberships: When you select Remove Gateway Membership, the Remove from Gateway section displays. From Gateway, you search for Gateways from in which members of this group policy should not be removed. From the result, click Add. The removed Gateways are shown in a table. Click the trash can to delete a Gateway from the list.
- Add Asset Group Memberships: When you select Add Asset Group Memberships, the Add to Asset Groups section displays. This section is where you search for Asset Groups to which members of this group policy should belong. You can set each user's Asset Role to set their permissions specific to Assets in this Asset Group, or you can use the user's default Asset Roles set in this group policy or on the Users & Security > Users page. An Asset Role is a predefined set of permissions regarding Asset management and usage. The added Asset Groups are shown in a table. To edit an Asset Group's settings, click the pencil. To delete the Asset Group from the list, click the trash can.
You can also apply an Asset Policy to manage user access to the Assets in this Asset Group by selecting Set on Assets instead uses the Asset Policy applied to the Asset itself.
Asset Policies are configured on the Asset Management > Asset Policies page and determine the times during which a user can access this Asset. An Asset Policy can also send a notification when it is accessed or can require approval to be accessed. If neither the user nor the Asset has an Asset Policy applied, this Asset can be accessed without restriction. - Remove Asset Group Memberships: When you select Remove Asset Group Memberships, the Remove From Asset Groups section displays. In Asset Group, you search for Asset Groups from which members of this group policy should be removed. From the result, click Add. The removed Asset Groups are shown in a table. To delete an Asset Group from the list, click the trash can.
- Add Vault Account Memberships: When you select Add Vault Account Memberships, the Add to Vault Accounts section displays. From Accounts, you search for an account, select the Vault Account Role, and then click Add to grant members of the policy access to the selected vault account. Users may have memberships added by other group policies. To see a full list, go to Vault > Accounts to see all members within each account. Users may be assigned one of two roles for using the vault account:
- Inject: (default value) Users with this role can use this account in Privileged Remote Access sessions.
- Inject and Checkout: Users with this role can use this account in Privileged Remote Access sessions and can check out the account on Admin. The Checkout permission has no effect on generic SSH accounts.
Enable the Add Vault Account Memberships permission to assign a Vault Account Role to a vault account in a group policy. The Vault Account Role is visible in the list of accounts added to the group policy.
- Add Vault Account Group Memberships: When you select Add Vault Account Group Membership, the Add To Vault Account Groups section displays. In Account Group, you search for an account group, select the Vault Account Role, and then click Add to grant members of the policy access to the group of vault accounts. Users may have memberships added by other group policies. View Vault > Account Groups to see all members within each group. Users may be assigned one of two roles for using the group of vault accounts:
- Inject: (default value) Users with this role can use this account in Privileged Remote Access sessions.
- Inject and Checkout: Users with this role can use this account in Privileged Remote Access sessions and can check out the account on Admin. The Checkout permission has no effect on generic SSH accounts.
Enable the Add Vault Account Group permission to assign a Vault Account Role to a group of vault accounts in a group policy. The Vault Account Role is visible in the list of account groups added to the group policy.
Export policy
You can export a session policy from one site and import those permissions into a policy on another site.
To export a saved policy file, do the following:
- Sign into app.beyondtrust.io.
The BeyondTrust Home page displays. - From the main menu, click Privileged Remote Access > Users & Security.
The User & Security page opens and the Users tab displays by default. - Click the Session Policies tab.
The Session Policies tab displays. - Edit an existing policy file, click the pencil.
- Scroll to the bottom of the page, click Export Policy, and save the file.
When you export a group policy, only the policy name, account settings, and permissions are exported. Policy members, team memberships, and Gateway memberships are not included in the export.
Import policy
You may import those policy settings to any other BeyondTrust site that supports session policy import.
To import a saved policy file, do the following:
- Sign into app.beyondtrust.io.
The BeyondTrust Home page displays. - From the main menu, click Privileged Remote Access > Users & Security.
The User & Security page opens and the Users tab displays by default. - Click the Session Policies tab.
The Session Policies tab displays. - Edit an existing policy file, click the pencil.
- Scroll to the bottom of the page, click + Select Policy File.
- From the Open dialog box, located the exported policy file. The default extension is .bgo.
- Select the exported policy file, click Open.
- Once the policy file is uploaded, the Edit Session Policy page displays, which allows you to make modifications. After the modifications are made, click Save.
When you import a policy file to an existing group policy it overwrites any previously defined permissions, with the exception of policy members, team memberships, and Gateway memberships.
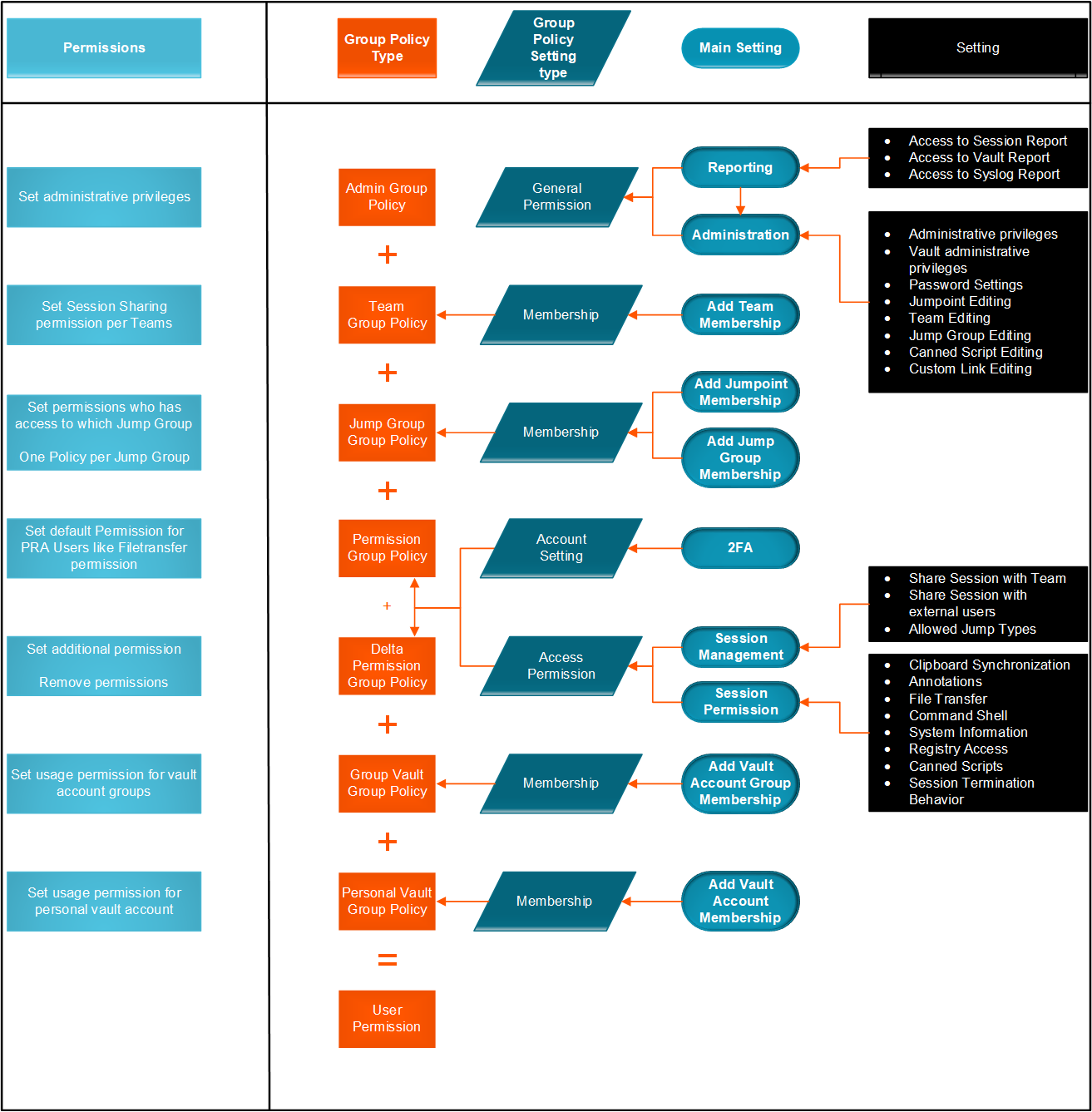
Sample policy matrix
The diagram below is an example of how multiple policies can work together.
Updated about 2 months ago
