Ansible | PS
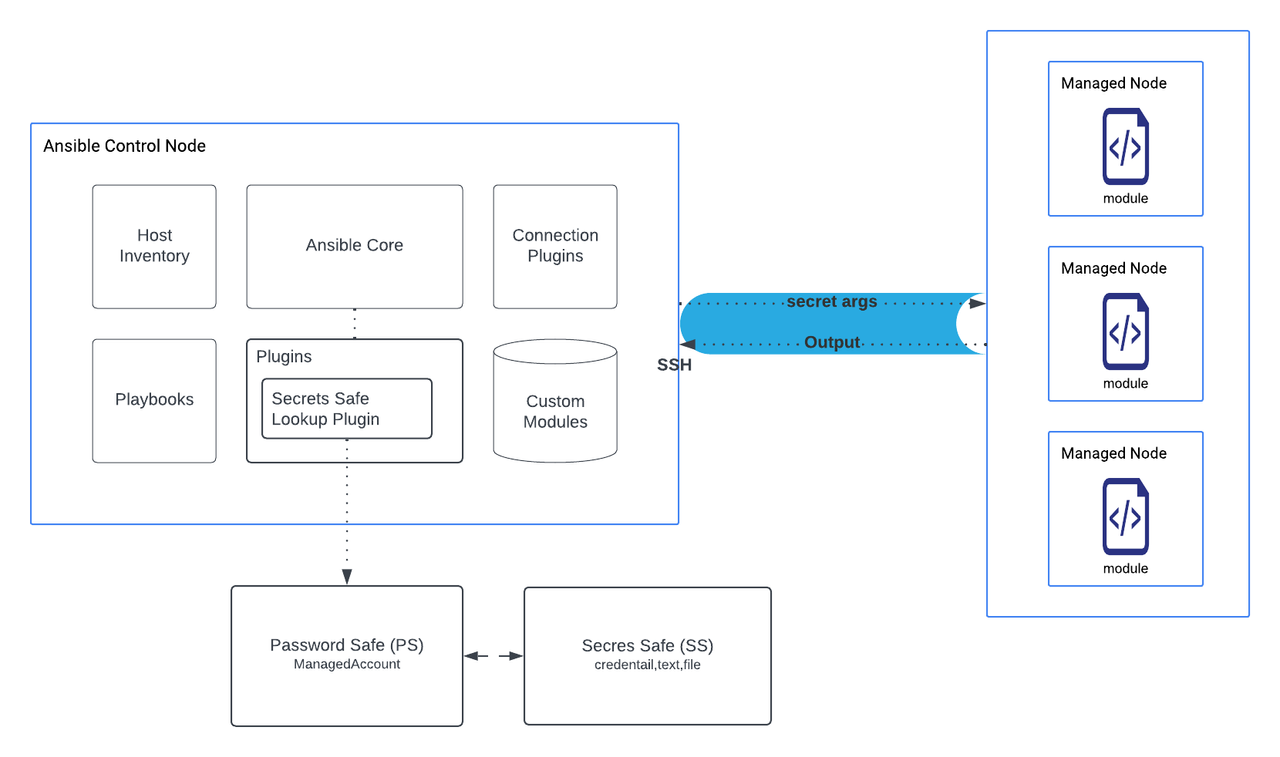
Ansible is an open-source software provisioning, configuration management, and application-deployment tool that enables IaC (infrastructure as code). Password Safe's integration with Ansible provides an easy to use method for users to secure and manage their Ansible related secrets for automated workflows. Secrets Safe users can leverage this integration for Continuous Integration and Continuous Deployment (CI/CD) and DevOps workflows.
The Secrets Safe Lookup plugin can be configured to retrieve ASCII secrets from Secrets Safe.
Prerequisites
The Secrets Safe Lookup plugin supports the following software, features, and configurations:
- Supports retrieval of secrets from BeyondInsight and Password Safe version 23.1 or later releases.
- Supports OAuth client secret for authentication across applications and services.
- Supports managed account password retrieval.
- Is compatible with Ansible core v2.14 and later releases.
- Is compatible with Python v3.11 and later releases.
- The Secrets Safe instance must be preconfigured with the secret in question, and an account must be authorized to read it in order for this plugin to retrieve a secret.
Important information
- Do not log the secrets to stdout. Security-minded engineers must review playbooks composition before changes are run with access to secrets.
- Ansible writes lookup plugin arguments to stdout. Do not put secret text directly in the lookup plugin arguments. Use variables as an alternative.
Overview
The Secrets Safe Lookup plugin is named secrets_safe_lookup. It is designed to be run on an Ansible Control node (Linux). The lookup plugin is available from the Ansible Galaxy Registry.
For more information, see the Ansible Galaxy Registry.
General setup
- Create an API registration in BeyondInsight. Ensure the User password required option is disabled.
- Create or use an existing Secrets Safe group.
- Create or use an existing BeyondInsight user.
- Add API registration to the group.
- Add the user to the group.
- Add the Secrets Safe feature to the group. Assign read-only or full access based on your use case.
Managed accounts setup
- Create or use an existing access policy that has the View Password option enabled with the Auto Approve option selected.
- Add the All Managed Accounts Smart Group to the BeyondInsight group.
- Add the access policy to Password Safe role assigned to the All Managed Accounts Smart Group. Ensure that both Requestor and Approver are selected in the assigned role.
- Create or use an existing managed system.
- Create or use an existing managed account associated with the managed system.
- Configure the managed account with the API Enabled and Max Concurrent Requests Unlimited options selected.
Available Ansible collections
Installing collections from Ansible Galaxy
To install the collections, you can use the next command if the collection is on Ansible Galaxy repository:
ansible-galaxy collection install beyondtrust.secrets_safe
ansible-galaxy collection install beyondtrust.password_safeInstalling collection manually
If you have the collections downloaded locally, you can run the next command:
ansible-galaxy collection install beyondtrust-secrets_safe-<version>.tar.gz
ansible-galaxy collection install beyondtrust-password_safe-<version>.tar.gzIf it's not a fresh install, you would need to run the next command to update the collection to its latest version:
ansible-galaxy collection install --upgrade beyondtrust-secrets_safe-<version>.tar.gz
ansible-galaxy collection install --upgrade beyondtrust-password_safe-<version>.tar.gzwhere
If the installation is successful, run this command:
ansible-galaxy collection listAnd you should see the collection installed:
...
Collection Version
----------------------- -------
beyondtrust.secrets_safe 1.0.1
beyondtrust.password_safe 1.0.1
...Install required modules
To run the plugin in a playbook, you need to install modules using pip, with the file requirements.txt, found locally after installing the collection. Run the following command:
pip install -r ~/.ansible/collections/ansible_collections/beyondtrust/secrets_safe/requirements.txt
pip install -r ~/.ansible/collections/ansible_collections/beyondtrust/password_safe/requirements.txtSecrets Safe Ansible Collection Documentation
Use the Secrets Safe lookup plugin
Usage
- api_url
- description: BeyondTrust Password Safe API URL.
- type: string
- required: True
- api_version
- description: The recommended version is 3.1. If no version is specified, the default API version 3.0 is used.
- type: string
- required: False
- retrieval_type
- description: Type of secret to retrieve (use MANAGED_ACCOUNT or SECRET)
- type: string
- required: True
- api_key
- description: API Key. If not set, then client_id/client_secret become required. RunAs user should be provided along with API key, e.g:
- type: string
- required: False
- client_id
- description: API OAuth Client ID.
- type: string
- required: True
- client_secret
- description: API OAuth Client Secret.
- type: string
- required: True
- secret_list
- description: List of secrets (path/title,path/title) or managed accounts (ms/ma,ms/ma) to be retrieved, separated by a comma.
- type: string
- required: True
- certificate_path
- description: Password Safe API pfx Certificate Path. For use when authenticating using a Client Certificate.
- type: string
- required: False
- certificate_password
- description: Password Safe API pfx Certificate Password. For use when authenticating using a Client Certificate.
- type: string
- required: False
- verify_ca
- description: Indicates whether to verify the certificate authority on the Secrets Safe instance.
- type: boolean
- default: True
- required: False
- decrypt
- description: When true, returns the decrypted password field; when false, the password field is omitted, this option only applies when retrieval_type is set to SECRET.
- type: boolean
- default: True
- required: False
- rotate_on_checkin
description: If True, rotates the password on check-in, only applies when retrieval type is set to MANAGED_ACCOUNT
type: boolean
default: True
required: False
Example
"{{lookup('beyondTrust.secrets_safe.secrets_safe_lookup', api_url=apiURL, api_version='3.1', retrieval_type='SECRET', client_id=clientIdFromEnvVar, client_secret=secretFromEnvVar, secret_list=secretList, certificate_path=certificatePath, certificate_password=certificatePasswordFromEnVar, wantlist=False, verify_ca=True)}}"
Output
- description: list of retrieved secret(s) in the requested order.
- type: list
- elements: str
Example
export PASSWORD_SAFE_CLIENT_ID=********************
export PASSWORD_SAFE_CLIENT_SECRET=********************
export CERTIFICATE_PASSWORD=********************
export PASSWORD_SAFE_API_URL=https://example.com:443/BeyondTrust/api/public/v3
---
- name: book
hosts: localhost
connection: local
vars:
apiURL: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_API_URL') }}"
clientIdFromEnvVar: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_CLIENT_ID') }}"
secretFromEnvVar: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_CLIENT_SECRET') }}"
certificatePasswordFromEnVar: "{{ lookup('ansible.builtin.env', 'CERTIFICATE_PASSWORD') }}"
certificatePath: "<path>/ClientCertificate.pfx"
secretManagedAccounts: "fake_system/fake_ managed_account,fake_system/fake_managed_account01"
gotManagedAccount: "{{lookup('beyondTrust.secrets_safe.secrets_safe_lookup', api_url=apiURL, retrieval_type='MANAGED_ACCOUNT', client_id=clientIdFromEnvVar, client_secret=secretFromEnvVar, secret_list=secretManagedAccounts, certificate_path=certificatePath, certificate_password=certificatePasswordFromEnVar, wantlist=False)}}"
secretList: "fake_grp/credential,fake_grp/file"
gotSecrets: "{{lookup('beyondTrust.secrets_safe.secrets_safe_lookup', api_url=apiURL, api_version='3.1', retrieval_type='SECRET', client_id=clientIdFromEnvVar, client_secret=secretFromEnvVar, secret_list=secretList, certificate_path=certificatePath, certificate_password=certificatePasswordFromEnVar, wantlist=False, verify_ca=True)}}"
tasks:
- name: Display Retrieved Managed accounts
ansible.builtin.debug:
msg: "{{ gotManagedAccount }}"
- name: Display Retrieved Secrets
ansible.builtin.debug:
msg: "{{ gotSecrets }}"
Module: folders_create
Short Description
Create Folder in Beyondtrust Password Safe API.
Description
Creates a folder in the given folder name.
Parameters
| Name | Description | Type | Required | Default |
|---|---|---|---|---|
| client_id | API OAuth Client ID. | str | ✅ Yes | |
| client_secret | API OAuth Client Secret. | str | ✅ Yes | |
| api_url | BeyondTrust Password Safe API URL | str | ✅ Yes | |
| data | Folder data | dict | ✅ Yes | |
| log_level | Log file's log level (INFO, DEBUG, WARNING, ERROR). | str | ❌ No | DEBUG |
| log_file_name | Log file's name | str | ❌ No | ansible-collection-modules-logs |
| api_version | The recommended version is 3.1. If no version is specified, the default API version 3.0 will be used. | str | ❌ No | 3.0 |
| verify_ca | Verify CA parameter for SSL certificate validation. If set to False, SSL certificate validation will be disabled, which is insecure and exposes you to man-in-the-middle attacks. Only set to False for testing purposes in trusted environments. | bool | ❌ No | True |
Details of data object
| Name | Description | Type | Required | Default |
|---|---|---|---|---|
| name | The name of the folder | str | ✅ Yes | |
| description | The description of the folder | str | ❌ No | |
| user_group_id | the user group id. | int | ❌ No | |
| folder_name | The Name of the parent folder where folder will be created. | str | ✅ Yes |
Example- name: Create Folder beyondtrust.secrets_safe.folders_create: # PASSWORD_SAFE_API_URL, PASSWORD_SAFE_CLIENT_ID and PASSWORD_SAFE_CLIENT_SECRET are environment variables. api_url: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_API_URL') }}" client_id: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_CLIENT_ID') }}" client_secret: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_CLIENT_SECRET') }}" api_version: "3.0" data: name: "my_folder_name" folder_name: "parent_folder" description: "folder description"
Return values
| Name | Description | Returned | Type | Sample |
|---|---|---|---|---|
| id | Created Folder Id | success | str | 5601e126-9f1a-4c9c-9e4c-08db7741b532 |
| name | Created Folder Name | success | str | Folder Name |
Module: safes_create
Short Description
Create Safe in Beyondtrust Password Safe API.
Description
Creates a Safe.
Parameters
| Name | Description | Type | Required | Default |
|---|---|---|---|---|
| api_url | BeyondTrust Password Safe API URL. | str | ✅ Yes | |
| client_id | API OAuth Client ID | str | ✅ Yes | |
| client_secret | API OAuth Client Secret. | str | ✅ Yes | |
| api_url | BeyondTrust Password Safe API URL | str | ✅ Yes | |
| data | Safe data | dict | ✅ Yes | |
| log_level | Log file's log level (INFO, DEBUG, WARNING, ERROR). | str | ❌ No | DEBUG |
| log_file_name | Log file's name | str | ❌ No | ansible-collection-modules-logs |
| api_version | The recommended version is 3.1. If no version is specified, the default API version 3.0 will be used. | str | ❌ No | 3.0 |
| verify_ca | Verify CA parameter for SSL certificate validation. If set to False, SSL certificate validation will be disabled, which is insecure and exposes you to man-in-the-middle attacks. Only set to False for testing purposes in trusted environments. | bool | ❌ No | True |
Details of data object
| Name | Description | Type | Required | Default |
|---|---|---|---|---|
| name | The name of the Safe | str | ✅ Yes | |
| description | The description of the Safe | str | ❌ No |
Example- name: Create Safe beyondtrust.secrets_safe.safes_create: # PASSWORD_SAFE_API_URL, PASSWORD_SAFE_CLIENT_ID and PASSWORD_SAFE_CLIENT_SECRET are environment variables. api_url: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_API_URL') }}" client_id: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_CLIENT_ID') }}" client_secret: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_CLIENT_SECRET') }}" api_version: "3.0" data: name: "my_safe_name" description: "safe description"
Return values
| Name | Description | Returned | Type | Sample |
|---|---|---|---|---|
| id | Created Safes Id | success | str | 5601e126-9f1a-4c9c-9e4c-08db7741b532 |
| name | Created Safe Name | success | str | Safe Title |
Module: secrets_create
Short Description
Create secrets (credential, text, file) in Beyondtrust Password Safe API.
Description
Creates a secret (credential, text, file) in the given folder name.
Parameters
| Name | Description | Type | Required | Default |
|---|---|---|---|---|
| api_url | BeyondTrust Password Safe API URL. | str | ✅ Yes | |
| client_id | API OAuth Client ID | str | ✅ Yes | |
| client_secret | API OAuth Client Secret. | str | ✅ Yes | |
| data | Secret data | dict | ✅ Yes | |
| log_level | Log file's log level (INFO, DEBUG, WARNING, ERROR). | str | ❌ No | DEBUG |
| log_file_name | Log file's name | str | ❌ No | ansible-collection-modules-logs |
| api_version | The recommended version is 3.1. If no version is specified, the default API version 3.0 will be used. | str | ❌ No | 3.0 |
| verify_ca | Verify CA parameter for SSL certificate validation. If set to False, SSL certificate validation will be disabled, which is insecure and exposes you to man-in-the-middle attacks. Only set to False for testing purposes in trusted environments. | bool | ❌ No | True |
Details of data object
| Name | Description | Type | Required | Default |
|---|---|---|---|---|
| title | The full title of the secret | str | ✅ Yes | |
| description | The description of the secret | str | ❌ No | |
| owner_id | The ID of the owner | int | ❌ No | |
| owner_type | The type of the owner | str | ❌ No | |
| file_path | The path to the file for File Secrets | str | ❌ No | |
| username | The username for normal Secrets | str | ❌ No | |
| password | The password for normal Secrets | str | ❌ No | |
| password_rule_id | The ID of the password rule | str | ❌ No | |
| notes | Notes about the secret | str | ❌ No | |
| text | The text content for Text Secrets | str | ❌ No | |
| folder_name | The Name of the folder where secrets will be created. | str | ✅ Yes | |
| urls | BeyondTrust A list of URLs with this format. | list | ❌ No | |
| owners | A list of owners. | list | ✅ Yes |
Example- name: Create File Secret in PS beyondtrust.secrets_safe.secrets_create: # PASSWORD_SAFE_API_URL, PASSWORD_SAFE_CLIENT_ID and PASSWORD_SAFE_CLIENT_SECRET are environment variables. api_url: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_API_URL') }}" client_id: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_CLIENT_ID') }}" client_secret: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_CLIENT_SECRET') }}" api_version: "3.0" data: title: "Secret Title" username: "test_user" password: "Secret content" folder_name: "my_folder_name" description: "Folder Description" owner_id: 12 owner_type: "User" owners: - owner_id: 12 - name: Create Credential Secret in PS beyondtrust.secrets_safe.secrets_create: # PASSWORD_SAFE_API_URL, PASSWORD_SAFE_CLIENT_ID and PASSWORD_SAFE_CLIENT_SECRET are environment variables. api_url: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_API_URL') }}" client_id: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_CLIENT_ID') }}" client_secret: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_CLIENT_SECRET') }}" api_version: "3.0" data: title: "Secret Title" text: "Secret content" folder_name: "my_folder_name" description: "Folder Description" owner_id: 12 owner_type: "User" owners: - owner_id: 12 - name: Create Text Secret in PS beyondtrust.secrets_safe.secrets_create: # PASSWORD_SAFE_API_URL, PASSWORD_SAFE_CLIENT_ID and PASSWORD_SAFE_CLIENT_SECRET are environment variables. api_url: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_API_URL') }}" client_id: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_CLIENT_ID') }}" client_secret: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_CLIENT_SECRET') }}" api_version: "3.0" data: title: "Secret Title" file_path: "my_secret.txt" folder_name: "my_folder_name" description: "Folder Description" owner_id: 12 owner_type: "User" owners: - owner_id: 12
Return values
| Name | Description | Returned | Type | Sample |
|---|---|---|---|---|
| secret_id | Created Secret Id | success | str | 5601e126-9f1a-4c9c-9e4c-08db7741b532 |
| secret_name | Created Secret Name | success | str | Secret Title |
Lookup Plugins
Lookup Plugin: safes_list
Short Description
Retrieve safes list from Password Safe.
Description
Custom lookup plugin to fetch safes list from Password Safe.
Parameters
| Name | Description | Type | Required | Default |
|---|---|---|---|---|
| api_url | BeyondTrust Password Safe API URL. | str | ✅ Yes | |
| api_version | The recommended version is 3.1. If no version is specified, the default API version 3.0 will be used. | str | ❌ No | 3.0 |
| client_id | API OAuth Client ID | str | ✅ Yes | |
| client_secret | API OAuth Client Secret. | str | ✅ Yes | |
| log_level | Log file's log level (INFO, DEBUG, WARNING, ERROR). | str | ❌ No | DEBUG |
| log_file_name | Log file's name | str | ❌ No | ansible-collection-modules-logs |
| verify_ca | Verify CA parameter for SSL certificate validation. If set to False, SSL certificate validation will be disabled, which is insecure and exposes you to man-in-the-middle attacks. Only set to False for testing purposes in trusted environments. | bool | ❌ No | True |
| workgroup_id | The Workgroup ID, if want to search by Workgroup ID | N/A | ❌ No | |
| workgroup_name | The Workgroup name, if want to search by Workgroup name | N/A | ❌ No |
Example--- - vars: # PASSWORD_SAFE_API_URL, PASSWORD_SAFE_CLIENT_ID and PASSWORD_SAFE_CLIENT_SECRET are environment variables. api_url: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_API_URL') }}" client_id: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_CLIENT_ID') }}" client_secret: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_CLIENT_SECRET') }}" safes: "{{ lookup('beyondtrust.password_safe.safes_list', api_url=api_url, client_id=client_id, client_secret=client_secret) }}" tasks: - name: Print Safes list debug: msg: "{{ safes }}" - name: Print my_new_safe_name safe debug: msg: "{{ safes | selectattr('Name', 'equalto', 'my_new_safe_name') | first }}"
Return values
| Name | Description | Returned | Type | Sample |
|---|---|---|---|---|
| _list | list of all safes | str |
Lookup Plugin: folders_list
Short Description
Retrieve folders list from Password Safe.
Description
Custom lookup plugin to fetch folders list from Password Safe.
Parameters
| Name | Description | Type | Required | Default |
|---|---|---|---|---|
| api_url | BeyondTrust Password Safe API URL. | str | ✅ Yes | |
| api_version | The recommended version is 3.1. If no version is specified, the default API version 3.0 will be used. | str | ❌ No | 3.0 |
| client_id | API OAuth Client ID | str | ✅ Yes | |
| client_secret | API OAuth Client Secret. | str | ✅ Yes | |
| log_level | Log file's log level (INFO, DEBUG, WARNING, ERROR). | str | ❌ No | DEBUG |
| log_file_name | Log file's name | str | ❌ No | ansible-collection-modules-logs |
| verify_ca | Verify CA parameter for SSL certificate validation. If set to False, SSL certificate validation will be disabled, which is insecure and exposes you to man-in-the-middle attacks. Only set to False for testing purposes in trusted environments. | bool | ❌ No | True |
| workgroup_id | The Workgroup ID, if want to search by Workgroup ID | N/A | ❌ No | |
| workgroup_name | The Workgroup name, if want to search by Workgroup name | N/A | ❌ No |
Example--- - vars: # PASSWORD_SAFE_API_URL, PASSWORD_SAFE_CLIENT_ID and PASSWORD_SAFE_CLIENT_SECRET are environment variables. api_url: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_API_URL') }}" client_id: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_CLIENT_ID') }}" client_secret: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_CLIENT_SECRET') }}" folders: "{{ lookup('beyondtrust.password_safe.folders_list', api_url=api_url, client_id=client_id, client_secret=client_secret) }}" tasks: - name: Print Folders list debug: msg: "{{ folders }}" - name: Print folder2 folder debug: msg: "{{ folders | selectattr('Name', 'equalto', 'folder2') | first }}"
Return values
| Name | Description | Returned | Type | Sample |
|---|---|---|---|---|
| _list | list of all folders | str |
Lookup Plugin: secrets_safe_lookup
Short Description
Retrieve ASCII secrets from Secrets Safe.
Description
Retrieve ASCII secrets and managed account passwords from BeyondTrust Password Safe 23.1 or greater.
Parameters
| Name | Description | Type | Required | Default |
|---|---|---|---|---|
| api_url | BeyondTrust Password Safe API URL. | str | ✅ Yes | |
| api_version | The recommended version is 3.1. If no version is specified, the default API version 3.0 will be used. | str | ❌ No | 3.0 |
| api_key | "API Key. If not set, then client_id/client_secret become required. RunAs user should be provided along with API key: e.g: <key;runas=<user" | N/A | ❌ No | |
| retrieval_type | Type of secret to retrieve (use MANAGED_ACCOUNT or SECRET) | str | ✅ Yes | |
| client_id | API OAuth Client ID. Required only if api_key is not provided. | str | ❌ No | |
| client_secret | API OAuth Client Secret. Required only if api_key is not provided. | str | ❌ No | |
| certificate_path | Password Safe API pfx Certificate Path. For use when authenticating using a Client Certificate. | str | ❌ No | |
| certificate_password | Password Safe API pfx Certificate Password. For use when authenticating using a Client Certificate. | str | ❌ No | |
| secret_list | List of secrets (path/title) or managed accounts (ms/ma) to be retrieved, separated by comma. | str | ✅ Yes | |
| separator | Secrets path separator, that is: folder1/folder2 | str | ❌ No | |
| verify_ca | Verify CA parameter for SSL certificate validation. If set to False, SSL certificate validation will be disabled, which is insecure and exposes you to man-in-the-middle attacks. Only set to False for testing purposes in trusted environments. | bool | ❌ No | True |
| list_delimiter | List delimiter, e.g.: secret1,secret2,secret3. | str | ❌ No |
Example--- - vars: # PASSWORD_SAFE_API_URL, PASSWORD_SAFE_CLIENT_ID and PASSWORD_SAFE_CLIENT_SECRET are environment variables. api_url: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_API_URL') }}" client_id: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_CLIENT_ID') }}" client_secret: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_CLIENT_SECRET') }}" certificatePasswordFromEnVar: "{{ lookup('ansible.builtin.env', 'CERTIFICATE_PASSWORD') }}" certificatePath: "<path>/ClientCertificate.pfx" secretManagedAccounts: "fake_system/fake_managed_account,fake_system/fake_managed_account01" gotManagedAccount: "{{lookup('beyondTrust.secrets_safe.secrets_safe_lookup', api_url=api_url, retrieval_type='MANAGED_ACCOUNT', client_id=client_id, client_secret=client_secret, secret_list=secretManagedAccounts, certificate_path=certificatePath, certificate_password=certificatePasswordFromEnVar, wantlist=False)}}" secretList: "fake_grp/credential,fake_grp/file" gotSecrets: "{{lookup('beyondTrust.secrets_safe.secrets_safe_lookup', api_url=api_url, retrieval_type='SECRET', client_id=client_id, client_secret=client_secret, secret_list=secretList, certificate_path=certificatePath, certificate_password=certificatePasswordFromEnVar, wantlist=False, verify_ca=True)}}"
Return values
| Name | Description | Returned | Type | Sample |
|---|---|---|---|---|
| _list | list of retrieved secret(s) in the requested order | list |
Password Safe Ansible Collection Documentation
Module: assets_create
Short Description
Create Assets in Beyondtrust Password Safe API.
Description
Creates an asset.
Parameters
| Name | Description | Type | Required | Default |
|---|---|---|---|---|
| api_url | BeyondTrust Password Safe API URL. | str | ✅ Yes | |
| api_version | The recommended version is 3.1. If no version is specified, the default API version 3.0 will be used. | str | ❌ No | 3.0 |
| client_id | API OAuth Client ID | str | ✅ Yes | |
| client_secret | API OAuth Client Secret. | str | ✅ Yes | |
| log_level | Log file's log level (INFO, DEBUG, WARNING, ERROR). | str | ❌ No | DEBUG |
| log_file_name | Log file's name | str | ❌ No | ansible-collection-modules-logs |
| verify_ca | Verify CA parameter for SSL certificate validation. If set to False, SSL certificate validation will be disabled, which is insecure and exposes you to man-in-the-middle attacks. Only set to False for testing purposes in trusted environments. | bool | ❌ No | True |
| data | Asset data. | dict | ✅ Yes |
Details of data object
| Name | Description | Type | Required | Default |
|---|---|---|---|---|
| workgroup_id | workgroup id. | int | ❌ No | |
| workgroup_name | workgroup name. | str | ❌ No | |
| ip_address | Asset IP address | str | ✅ Yes | |
| asset_name | Asset name. If not given, a padded IP address is used. | str | ✅ Yes | |
| dns_name | Asset DNS name | str | ❌ No | |
| domain_name | Asset domain name | str | ❌ No | |
| mac_address | Asset MAC address | str | ❌ No | |
| asset_type | Asset type | str | ❌ No | |
| description | Asset description | list | ❌ No | |
| operating_system | Asset operating system | list | ❌ No |
Example- name: Create Asset beyondtrust.password_safe.assets_create: # PASSWORD_SAFE_API_URL, PASSWORD_SAFE_CLIENT_ID and PASSWORD_SAFE_CLIENT_SECRET are environment variables. api_url: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_API_URL') }}" client_id: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_CLIENT_ID') }}" client_secret: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_CLIENT_SECRET') }}" api_version: "3.0" verify_ca: true data: workgroup_id: 10 ip_address: "192.168.1.100" asset_name: "my_asset" dns_name: "my-asset.example.com" domain_name: "example.com" mac_address: "00:1A:2B:3C:4D:5E" asset_type: "Server" description: "Linux application server" operating_system: "Ubuntu 22.04 LTS"
Return values
| Name | Description | Returned | Type | Sample |
|---|---|---|---|---|
| id | Created Asset Id. | success | int | 123 |
| name | Created Asset Name | success | str | Asset Name |
Module: workgroups_create
Short Description
Create Workgroup in Beyondtrust Password Safe API.
Description
Creates a workgroup.
Parameters
| Name | Description | Type | Required | Default |
|---|---|---|---|---|
| api_url | BeyondTrust Password Safe API URL. | str | ✅ Yes | |
| api_version | The recommended version is 3.1. If no version is specified, the default API version 3.0 will be used. | str | ❌ No | 3.0 |
| client_id | API OAuth Client ID | str | ✅ Yes | |
| client_secret | API OAuth Client Secret. | str | ✅ Yes | |
| log_level | Log file's log level (INFO, DEBUG, WARNING, ERROR). | str | ❌ No | DEBUG |
| log_file_name | Log file's name | str | ❌ No | ansible-collection-modules-logs |
| verify_ca | Verify CA parameter for SSL certificate validation. If set to False, SSL certificate validation will be disabled, which is insecure and exposes you to man-in-the-middle attacks. Only set to False for testing purposes in trusted environments. | bool | ❌ No | True |
| data | Workgroup data. | dict | ✅ Yes |
Details of data object
| Name | Description | Type | Required | Default |
|---|---|---|---|---|
| name | The name of the workgroup | str | ✅ Yes | |
| organization_id | Organization id | str | ❌ No |
Example- name: Create workgroup beyondtrust.password_safe.workgroups_create: # PASSWORD_SAFE_API_URL, PASSWORD_SAFE_CLIENT_ID and PASSWORD_SAFE_CLIENT_SECRET are environment variables. api_url: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_API_URL') }}" client_id: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_CLIENT_ID') }}" client_secret: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_CLIENT_SECRET') }}" api_version: "3.0" verify_ca: true data: name: "organization_name"
Return values
| Name | Description | Returned | Type | Sample |
|---|---|---|---|---|
| id | Created Workgroup Id | success | str | 5601e126-9f1a-4c9c-9e4c-08db7741b532 |
| name | Created Workgroup name | success | str | Workgroup Name |
Module: managed_systems_create_by_workgroup_id
Short Description
Create Managed System by Workgroup Id in Beyondtrust Password Safe API.
Description
Creates a Managed System by Workgroup Id.
Parameters
| Name | Description | Type | Required | Default |
|---|---|---|---|---|
| api_url | BeyondTrust Password Safe API URL. | str | ✅ Yes | |
| api_version | The recommended version is 3.1. If no version is specified, the default API version 3.0 will be used. | str | ❌ No | 3.0 |
| client_id | API OAuth Client ID | str | ✅ Yes | |
| client_secret | API OAuth Client Secret. | str | ✅ Yes | |
| log_level | Log file's log level (INFO, DEBUG, WARNING, ERROR). | str | ❌ No | DEBUG |
| log_file_name | Log file's name | str | ❌ No | ansible-collection-modules-logs |
| verify_ca | Verify CA parameter for SSL certificate validation. If set to False, SSL certificate validation will be disabled, which is insecure and exposes you to man-in-the-middle attacks. Only set to False for testing purposes in trusted environments. | bool | ❌ No | True |
| data | Managed System data | dict | ✅ Yes |
Details of data object
| Name | Description | Type | Required | Default |
|---|---|---|---|---|
| workgroup_id | workgroup id. | int | ✅ Yes | |
| entity_type_id | ID of the entity type | int | ✅ Yes | |
| host_name | Host name of the managed system | str | ✅ Yes | |
| ip_address | IP address of the managed system | str | ✅ Yes | |
| dns_name | DNS name of the managed system | str | ✅ Yes | |
| domain_name | Asset domain name | str | ❌ No | |
| instance_name | Instance name of the managed system | str | ❌ No | |
| forest_name | Forest name for the managed system | str | ❌ No | |
| platform_id | ID of the managed system platform | int | ✅ Yes | |
| net_bios_name | NetBIOS name of the managed system | str | ❌ No | |
| contact_email | Contact email address (max length 1000) | str | ✅ Yes | |
| description | Description of the managed system (max length 255) | str | ❌ No | |
| timeout | Connection timeout in seconds before a slow or unresponsive connection fails. | int | ❌ No | |
| password_rule_id | ID of the default password rule assigned to managed accounts created under this managed system. | int | ❌ No | |
| account_name_format | Format for the account name. | int | ✅ Yes | |
| oracle_internet_directory_service_name | Oracle Internet Directory service name. | str | ❌ No | |
| release_duration | Default release duration in minutes. | int | ❌ No | |
| max_release_duration | Default maximum release duration in minutes. | int | ❌ No | |
| isa_release_duration | Default Information Systems Administrator (ISA) release duration in minutes. | int | ❌ No | |
| auto_management_flag | True if password auto-management is enabled, otherwise false. | bool | ❌ No | |
| check_password_flag | True to enable password testing, otherwise false. | bool | ❌ No | |
| change_password_after_any_release_flag | True to change passwords on release of a request, otherwise false. | bool | ❌ No | |
| reset_password_on_mismatch_flag | True to queue a password change when scheduled password test fails, otherwise false. | bool | ❌ No | |
| change_frequency_type | The change frequency for scheduled password changes (first, last, xdays). | str | ❌ No | |
| change_frequency_days | Number of days for xdays frequency. | int | ❌ No | |
| change_time | UTC time of day scheduled password changes take place (24hr format 00:00-23:59). | str | ❌ No | |
| remote_client_type | The type of remote client to use. | str | ❌ No | |
| is_application_host | True if the managed system can be used as an application host, otherwise false. | bool | ❌ No | |
| access_url | Access URL for the managed system. | str | ❌ No | |
| is_default_instance | True if this is the default instance, otherwise false. | bool | ❌ No | |
| use_ssl | True to use SSL for connections, otherwise false. | bool | ❌ No | |
| port | The port used to connect to the host. | int | ❌ No | |
| ssh_key_enforcement_mode | Enforcement mode for SSH host keys (0- None, 1 -Auto, 2- Strict). | int | ❌ No | |
| ssh_key_enforcement_mode | Enforcement mode for SSH host keys (0- None, 1- Auto, 2- Strict). | int | ❌ No | |
| login_account_id | ID of the functional account used for SSH Session logins. | int | ❌ No | |
| oracle_internet_directory_id | Oracle Internet Directory ID. | str | ❌ No | |
| functional_account_id | ID of the functional account used for local managed account password changes. | int | ❌ No | |
| elevation_command | Elevation command to use (sudo, pbrun, pmrun). | str | ❌ No | |
| application_host_id | Managed system ID of the target application host. | int | ❌ No |
Example- name: Create Managed System beyondtrust.password_safe.managed_systems_create_by_workgroup_id: # PASSWORD_SAFE_API_URL, PASSWORD_SAFE_CLIENT_ID and PASSWORD_SAFE_CLIENT_SECRET are environment variables. api_url: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_API_URL') }}" client_id: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_CLIENT_ID') }}" client_secret: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_CLIENT_SECRET') }}" api_version: "3.0" verify_ca: true data: workgroup_id: 55 entity_type_id: 1 host_name: "test-server-01" ip_address: "192.168.1.100" dns_name: "test-server-01.example.com" instance_name: "SQLInstance1" template: "Standard" forest_name: "example.local" platform_id: 1 net_bios_name: "TESTSRV01" contact_email: "[email protected]" description: "Test SQL Server" timeout: 60 password_rule_id: 0 account_name_format: 1 oracle_internet_directory_service_name: "OIDService" release_duration: 180 max_release_duration: 1440 isa_release_duration: 120 auto_management_flag: false check_password_flag: true change_password_after_any_release_flag: false reset_password_on_mismatch_flag: true change_frequency_type: "xdays" change_frequency_days: 30 change_time: "02:00" remote_client_type: "EPM" is_application_host: false access_url: "https://test-server-01.example.com" is_default_instance: true use_ssl: true port: 1433 ssh_key_enforcement_mode: 0 dss_key_rule_id: 0 login_account_id: 0 oracle_internet_directory_id: "2a1ce180-2ae7-470a-9dda-1a8935407a1b" functional_account_id: 4 elevation_command: "sudo" application_host_id: 5001
Return values
| Name | Description | Returned | Type | Sample |
|---|---|---|---|---|
| id | Created Managed System Id | success | int | 123 |
| name | Created Managed System Name | success | str | Managed System Name |
Module: managed_accounts_create
Short Description
Create Managed Accounts in Beyondtrust Password Safe API.
Description
Creates a managed account.
Parameters
| Name | Description | Type | Required | Default |
|---|---|---|---|---|
| api_url | BeyondTrust Password Safe API URL. | str | ✅ Yes | |
| api_version | The recommended version is 3.1. If no version is specified, the default API version 3.0 will be used. | str | ❌ No | 3.0 |
| client_id | API OAuth Client ID | str | ✅ Yes | |
| client_secret | API OAuth Client Secret. | str | ✅ Yes | |
| log_level | Log file's log level (INFO, DEBUG, WARNING, ERROR). | str | ❌ No | DEBUG |
| log_file_name | Log file's name | str | ❌ No | ansible-collection-modules-logs |
| verify_ca | Verify CA parameter for SSL certificate validation. If set to False, SSL certificate validation will be disabled, which is insecure and exposes you to man-in-the-middle attacks. Only set to False for testing purposes in trusted environments. | bool | ❌ No | True |
| data | Managed Account data | dict | ✅ Yes |
Details of data object
| Name | Description | Type | Required | Default |
|---|---|---|---|---|
| managed_system_name | Managed System Name | str | ✅ Yes | |
| account_name | Account name | str | ❌ No | |
| password | Account password | str | ✅ Yes | |
| domain_name | Asset domain name | str | ❌ No | |
| user_principal_name | User Principal Name | str | ❌ No | |
| sam_account_name | The Active Directory SAM account name | str | ❌ No | |
| platform_id | ID of the managed system platform | int | ❌ No | |
| distinguished_name | The LDAP distinguished name | str | ❌ No | |
| private_key | DSS private key | str | ❌ No | |
| passphrase | DSS passphrase | str | ❌ No | |
| password_fallback_flag | Flag to allow password fallback | bool | ❌ No | False |
| login_account_flag | Indicates if this is a login account | bool | ❌ No | |
| account_name_format | Format for the account name. | int | ❌ No | |
description Description of the account. | Oracle Internet Directory service name. | str | ❌ No | |
| password_rule_id | Identifier of the password rule. | int | ❌ No | 0 |
| api_enabled | Indicates if API access is enabled. | bool | ❌ No | False |
| release_notification_email | Email address for release notifications. | int | ❌ No | 120 |
| max_release_duration | Default maximum release duration in minutes. | int | ❌ No | 525600 |
| change_services_flag | Indicates if services should be changed when the password is updated. | ❌ No | ||
| restart_services_flag | Indicates if services should be restarted after password changes. | ❌ No | ||
| change_tasks_flag | Indicates if tasks should be updated when the password changes. | ❌ No | ||
| release_duration | Default release duration in minutes. | int | ❌ No | |
| isa_release_duration | Default Information Systems Administrator (ISA) release duration in minutes. | int | ❌ No | 120 |
| max_concurrent_requests | Maximum number of concurrent password requests for this account. | int | ❌ No | 1 |
| auto_management_flag | True if password auto-management is enabled, otherwise false. | bool | ❌ No | False |
| dss_auto_management_flag | True if DSS key auto-management is enabled, otherwise false | bool | ❌ No | False |
| check_password_flag | True to enable password testing, otherwise false. | bool | ❌ No | False |
| change_password_after_any_release_flag | True to change passwords on release of a request, otherwise false. | bool | ❌ No | False |
| reset_password_on_mismatch_flag | True to queue a password change when scheduled password test fails, otherwise false. | bool | ❌ No | False |
| next_change_date | Date of the next scheduled password change. | str | ❌ No | |
| use_own_credentials | True if the current account credentials should be used during change operations, otherwise false. | bool | ❌ No | |
| change_iis_app_pool_flag | Indicates if IIS application pools should be updated after password changes. | bool | ❌ No | |
| restart_iis_app_pool_flag | True if IIS application pools should be restarted after the run as password is changed, otherwise false. | bool | ❌ No | |
| workgroup_id | ID of the assigned Workgroup. | ❌ No | ||
| change_windows_auto_logon_flag | True if Windows Auto Logon should be updated with the new password after a password change, otherwise false. | bool | ❌ No | False |
| change_com_plus_flag | True if COM+ Apps should be updated with the new password after a password change, otherwise false. | bool | ❌ No | False |
| change_dcom_flag | True if DCOM Apps should be updated with the new password after a password change, otherwise false. | bool | ❌ No | False |
| change_scom_flag | True if SCOM Identities should be updated with the new password after a password change, otherwise false. | bool | ❌ No | False |
| object_id | Unique object identifier. | ❌ No | ||
| change_frequency_type | The change frequency for scheduled password changes (first, last, xdays). | str | ❌ No | first |
| change_frequency_days | Number of days for xdays frequency. | int | ❌ No | |
| change_time | UTC time of day scheduled password changes take place (24hr format 00:00-23:59). | str | ❌ No |
Example- name: Create Managed Accounts beyondtrust.password_safe.managed_accounts_create: # PASSWORD_SAFE_API_URL, PASSWORD_SAFE_CLIENT_ID and PASSWORD_SAFE_CLIENT_SECRET are environment variables. api_url: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_API_URL') }}" client_id: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_CLIENT_ID') }}" client_secret: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_CLIENT_SECRET') }}" api_version: "3.0" verify_ca: true data: managed_system_name: "System Name" account_name: "example_account" password: "SomePasswordValue123!" domain_name: "example.com" user_principal_name: "[email protected]" sam_account_name: "EXAMPLE\\user" distinguished_name: "CN=User Example,OU=Users,DC=example,DC=com" private_key: "-----BEGIN PRIVATE KEY-----\nMIIEvQIBADANBgkqhkiG9...\n-----END PRIVATE KEY-----" passphrase: "MySecurePassphrase" password_fallback_flag: true login_account_flag: false description: "This is an example managed account" password_rule_id: 42 api_enabled: true release_notification_email: "[email protected]" change_services_flag: true restart_services_flag: false change_tasks_flag: true release_duration: 180 max_release_duration: 1440 isa_release_duration: 120 max_concurrent_requests: 3 auto_management_flag: false dss_auto_management_flag: false check_password_flag: true reset_password_on_mismatch_flag: true change_password_after_any_release_flag: false change_frequency_type: "xdays" change_frequency_days: 30 change_time: "02:00" next_change_date: "2025-10-13" use_own_credentials: false change_iis_app_pool_flag: true restart_iis_app_pool_flag: true workgroup_id: 501 change_windows_auto_logon_flag: false change_com_plus_flag: true change_dcom_flag: false change_scom_flag: false object_id: "d27fee10-30b2-46ee-9d61-192c34fb2bfd"
Return values
| Name | Description | Returned | Type | Sample |
|---|---|---|---|---|
| id | Created Managed Account Id | success | int | 61 |
| name | Created Managed Account Name | success | str | Managed Account Name |
Module: functional_accounts_create
Short Description
Create Functional Account in Beyondtrust Password Safe API.
Description
Creates a functional account.
Parameters
| Name | Description | Type | Required | Default |
|---|---|---|---|---|
| api_url | BeyondTrust Password Safe API URL. | str | ✅ Yes | |
| api_version | The recommended version is 3.1. If no version is specified, the default API version 3.0 will be used. | str | ❌ No | 3.0 |
| client_id | API OAuth Client ID | str | ✅ Yes | |
| client_secret | API OAuth Client Secret. | str | ✅ Yes | |
| log_level | Log file's log level (INFO, DEBUG, WARNING, ERROR). | str | ❌ No | DEBUG |
| log_file_name | Log file's name | str | ❌ No | ansible-collection-modules-logs |
| verify_ca | Verify CA parameter for SSL certificate validation. If set to False, SSL certificate validation will be disabled, which is insecure and exposes you to man-in-the-middle attacks. Only set to False for testing purposes in trusted environments. | bool | ❌ No | True |
| data | Functional Account data | dict | ✅ Yes |
Details of data object
| Name | Description | Type | Required | Default |
|---|---|---|---|---|
| functional_account_id | Functional Account ID | str | ❌ No | |
| platform_id | Platform ID | int | ✅ Yes | |
| domain_name | Domain name | str | ❌ No | |
| account_name | Account Name | str | ✅ Yes | |
| display_name | Display Name | str | ❌ No | |
| password | Password | str | ❌ No | |
| private_key | Private Key | str | ❌ No | |
| private_key | Private Key | str | ❌ No | |
| description | Description | str | ❌ No | |
| elevation_command | Elevation Command | str | ❌ No | |
| tenant_id | Tenant ID | str | ❌ No | |
| object_id | Object ID | str | ❌ No | |
| secret | Secret | str | ❌ No | |
| service_account_email | Service Account Email | str | ❌ No | |
| azure_instance | Azure Instance (AzurePublic or AzureUsGovernment) | str | ❌ No |
Example- name: Create Functional account beyondtrust.password_safe.functional_accounts_create: # PASSWORD_SAFE_API_URL, PASSWORD_SAFE_CLIENT_ID and PASSWORD_SAFE_CLIENT_SECRET are environment variables. api_url: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_API_URL') }}" client_id: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_CLIENT_ID') }}" client_secret: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_CLIENT_SECRET') }}" api_version: "3.0" verify_ca: true data: platform_id: 123 account_name: "my_account" domain_name: "example.com" display_name: "My Account Display Name" password: "SomePasswordValue" private_key: "-----BEGIN PRIVATE KEY-----\nMIIEvQIBADANBgkqhkiG9...\n-----END PRIVATE KEY-----" passphrase: "MyPassphrase" description: "This is an example account description" elevation_command: "sudo su -" tenant_id: "a3f2c5e8-47b0-4b3f-8e9a-12c456789abc" object_id: "d47a9b1e-9f32-4c2e-8a3d-9e1b5f7f1c23" secret: "SomeSecretValue" service_account_email: "[email protected]" azure_instance: "AzurePublic"
Return values
| Name | Description | Returned | Type | Sample |
|---|---|---|---|---|
| id | Created Functional Account Id | success | int | 61 |
| name | Created Functional Account Name | success | str | Account Name |
Module: databases_create
Short Description
Create Database in Beyondtrust Password Safe API.
Description
Creates a Database.
Parameters
| Name | Description | Type | Required | Default |
|---|---|---|---|---|
| api_url | BeyondTrust Password Safe API URL. | str | ✅ Yes | |
| api_version | The recommended version is 3.1. If no version is specified, the default API version 3.0 will be used. | str | ❌ No | 3.0 |
| client_id | API OAuth Client ID | str | ✅ Yes | |
| client_secret | API OAuth Client Secret. | str | ✅ Yes | |
| log_level | Log file's log level (INFO, DEBUG, WARNING, ERROR). | str | ❌ No | DEBUG |
| log_file_name | Log file's name | str | ❌ No | ansible-collection-modules-logs |
| verify_ca | Verify CA parameter for SSL certificate validation. If set to False, SSL certificate validation will be disabled, which is insecure and exposes you to man-in-the-middle attacks. Only set to False for testing purposes in trusted environments. | bool | ❌ No | True |
| data | Database data | dict | ✅ Yes |
Details of data object
| Name | Description | Type | Required | Default |
|---|---|---|---|---|
| asset_id | The Asset Id. | int | ✅ Yes | |
| platform_id | Platform ID | int | ✅ Yes | |
| port | The database port. | int | ✅ Yes | |
| instance_name | Name of the database instance. Required when IsDefaultInstance is false. Max string length is 100. | str | ❌ No | |
| is_default_instance | True if the database instance is the default instance, otherwise false. | bool | ❌ No | |
| version | The database version. Max string value is 20. | str | ❌ No | |
| template | The database connection template. | str | ❌ No |
Example- name: Create Database beyondtrust.password_safe.databases_create: # PASSWORD_SAFE_API_URL, PASSWORD_SAFE_CLIENT_ID and PASSWORD_SAFE_CLIENT_SECRET are environment variables. api_url: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_API_URL') }}" client_id: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_CLIENT_ID') }}" client_secret: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_CLIENT_SECRET') }}" api_version: "3.0" verify_ca: true data: asset_id=1 platform_id=9 port=1 instance_name="data base name" is_default_instance=false version="1.2" template=""
Return values
| Name | Description | Returned | Type | Sample |
|---|---|---|---|---|
| id | Created Database Instance Id | success | int | 123 |
| name | Created Database Instance Name | success | str | Database Name |
Module: managed_systems_create_by_database_id
Short Description
Create Managed System by Database Id in Beyondtrust Password Safe API.
Description
Creates a Managed System by Database Id.
Parameters
| Name | Description | Type | Required | Default |
|---|---|---|---|---|
| api_url | BeyondTrust Password Safe API URL. | str | ✅ Yes | |
| api_version | The recommended version is 3.1. If no version is specified, the default API version 3.0 will be used. | str | ❌ No | 3.0 |
| client_id | API OAuth Client ID | str | ✅ Yes | |
| client_secret | API OAuth Client Secret. | str | ✅ Yes | |
| log_level | Log file's log level (INFO, DEBUG, WARNING, ERROR). | str | ❌ No | DEBUG |
| log_file_name | Log file's name | str | ❌ No | ansible-collection-modules-logs |
| verify_ca | Verify CA parameter for SSL certificate validation. If set to False, SSL certificate validation will be disabled, which is insecure and exposes you to man-in-the-middle attacks. Only set to False for testing purposes in trusted environments. | bool | ❌ No | True |
| data | Managed System data | dict | ✅ Yes |
Details of data object
| Name | Description | Type | Required | Default |
|---|---|---|---|---|
| database_id | The ID of the database. | int | ✅ Yes | |
| contact_email | Contact email address (max length 1000). | str | ✅ Yes | |
| Description of the managed system (max length 255). | The database port. | int | ✅ Yes | |
| timeout | Connection timeout in seconds before a slow or unresponsive connection fails (default 30). | str | ❌ No | |
| password_rule_id | ID of the default password rule assigned to managed accounts created under this managed system (default 0). | bool | ❌ No | |
| release_duration | Default release duration in minutes (range 1-525600, default 120). | str | ❌ No | 120 |
| max_release_duration | Default maximum release duration in minutes (range 1-525600, default 525600). | str | ❌ No | 525600 |
| isa_release_duration | Default Information Systems Administrator (ISA) release duration in minutes (range 1-525600, default 120). | int | ❌ No | 120 |
| auto_management_flag | True if password auto-management is enabled, otherwise false; can be set if Platform.AutoManagementFlag is true (default false). | bool | ❌ No | False |
| functional_account_id | ID of the functional account used for local managed account password changes. | int | ❌ No | |
| check_password_flag | True to enable password testing, otherwise false. | bool | ❌ No | |
| change_password_after_any_release_flag | True to change passwords on release of a request, otherwise false. | bool | ❌ No | |
| reset_password_on_mismatch_flag | True to queue a password change when scheduled password test fails, otherwise false. | bool | ❌ No | |
| change_frequency_type | The change frequency for scheduled password changes. | str | ❌ No | first |
| change_frequency_days | Number of days for xdays frequency. | int | ❌ No | |
| change_time | UTC time of day scheduled password changes take place (24hr format 00:00-23:59, default 23:30). | str | ❌ No | 23:30 |
Example- name: Create Managed System beyondtrust.password_safe.managed_systems_create_by_database_id: # PASSWORD_SAFE_API_URL, PASSWORD_SAFE_CLIENT_ID and PASSWORD_SAFE_CLIENT_SECRET are environment variables. api_url: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_API_URL') }}" client_id: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_CLIENT_ID') }}" client_secret: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_CLIENT_SECRET') }}" api_version: "3.0" verify_ca: true data: database_id: 2 contact_email: "[email protected]" description: "Test SQL Server" timeout: 60 password_rule_id: 0 release_duration: 180 max_release_duration: 1440 isa_release_duration: 120 auto_management_flag: false functional_account_id: 0 check_password_flag: true change_password_after_any_release_flag: false reset_password_on_mismatch_flag: true change_frequency_type: "xdays" change_frequency_days: 30 change_time: "02:00"
Return values
| Name | Description | Returned | Type | Sample |
|---|---|---|---|---|
| id | Created Managed System Id | success | int | 123 |
| name | Created Managed System Name | success | str | Managed System Name |
Module: managed_systems_create_by_asset_id
Short Description
Create Managed System by Asset Id in Beyondtrust Password Safe API.
Description
Creates a Managed System by Asset Id.
Parameters
| Name | Description | Type | Required | Default |
|---|---|---|---|---|
| api_url | BeyondTrust Password Safe API URL. | str | ✅ Yes | |
| api_version | The recommended version is 3.1. If no version is specified, the default API version 3.0 will be used. | str | ❌ No | 3.0 |
| client_id | API OAuth Client ID | str | ✅ Yes | |
| client_secret | API OAuth Client Secret. | str | ✅ Yes | |
| log_level | Log file's log level (INFO, DEBUG, WARNING, ERROR). | str | ❌ No | DEBUG |
| log_file_name | Log file's name | str | ❌ No | ansible-collection-modules-logs |
| verify_ca | Verify CA parameter for SSL certificate validation. If set to False, SSL certificate validation will be disabled, which is insecure and exposes you to man-in-the-middle attacks. Only set to False for testing purposes in trusted environments. | bool | ❌ No | True |
| data | Managed System data | dict | ✅ Yes |
Details of data object
| Name | Description | Type | Required | Default |
|---|---|---|---|---|
| asset_id | The ID of the Asset. | int | ✅ Yes | |
| platform_id | ID of the managed system platform (required). | int | ✅ Yes | |
| contact_email | Contact email address (max length 1000). | str | ✅ Yes | |
| description | Description of the managed system (max length 255). | int | ✅ Yes | |
| port | The port used to connect to the host, if null and Platform.PortFlag is true, uses Platform.DefaultPort. | int | ❌ No | |
| timeout | Connection timeout in seconds before a slow or unresponsive connection fails (default 30). | str | ❌ No | 30 |
| ssh_key_enforcement_mode | Enforcement mode for SSH host keys (0- None, 1- Auto, 2- Strict; default 0). | int | ❌ No | 0 |
| password_rule_id | ID of the default password rule assigned to managed accounts created under this managed system (default 0). | int | ❌ No | 0 |
| dss_key_rule_id | ID of the default DSS key rule assigned to managed accounts; can be set when Platform.DSSFlag is true (default 0). | int | ❌ No | 0 |
| login_account_id | ID of the functional account used for SSH Session logins; can be set if Platform.LoginAccountFlag is true. | int | ❌ No | 0 |
| release_duration | Default release duration in minutes (range 1-525600, default 120). | str | ❌ No | 120 |
| max_release_duration | Default maximum release duration in minutes (range 1-525600, default 525600). | str | ❌ No | 525600 |
| isa_release_duration | Default Information Systems Administrator (ISA) release duration in minutes (range 1-525600, default 120). | int | ❌ No | 120 |
| auto_management_flag | True if password auto-management is enabled, otherwise false; can be set if Platform.AutoManagementFlag is true (default false). | bool | ❌ No | False |
| functional_account_id | ID of the functional account used for local managed account password changes. | int | ❌ No | |
| elevation_command | Elevation command to use (sudo, pbrun, pmrun); can be set if Platform.SupportsElevationFlag is true. | str | ❌ No | |
| check_password_flag | True to enable password testing, otherwise false. | bool | ❌ No | |
| change_password_after_any_release_flag | True to change passwords on release of a request, otherwise false. | bool | ❌ No | |
| reset_password_on_mismatch_flag | True to queue a password change when scheduled password test fails, otherwise false. | bool | ❌ No | |
| change_frequency_type | The change frequency for scheduled password changes. | str | ❌ No | first |
| change_frequency_days | Number of days for xdays frequency. | int | ❌ No | |
| change_time | UTC time of day scheduled password changes take place (24hr format 00:00-23:59, default 23:30). | str | ❌ No | 23:30 |
| remote_client_type | The type of remote client to use (None, EPM). | str | ❌ No | |
| application_host_id | Managed system ID of the target application host (required when Platform.RequiresApplicationHost is true). | int | ❌ No | |
| is_application_host | True if the managed system can be used as an application host. | bool | ❌ No |
Example- name: Create Managed System beyondtrust.password_safe.managed_systems_create_by_asset_id: # PASSWORD_SAFE_API_URL, PASSWORD_SAFE_CLIENT_ID and PASSWORD_SAFE_CLIENT_SECRET are environment variables. api_url: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_API_URL') }}" client_id: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_CLIENT_ID') }}" client_secret: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_CLIENT_SECRET') }}" api_version: "3.0" verify_ca: true data: asset_id: 48 platform_id: 1 contact_email: "[email protected]" description: "Linux Test Server" release_duration: 125 max_release_duration: 1440 isa_release_duration: 125 password_rule_id: 0 check_password_flag: true change_password_after_any_release_flag: false reset_password_on_mismatch_flag: true change_frequency_type: "xdays" change_frequency_days: 30 change_time: "02:00" is_application_host: false timeout: 60 port: 22 ssh_key_enforcement_mode: 1 dss_key_rule_id: 0 login_account_id: 0 auto_management_flag: false functional_account_id: 4 elevation_command: "sudo" remote_client_type: "EPM" application_host_id: 3001
Return values
| Name | Description | Returned | Type | Sample |
|---|---|---|---|---|
| id | Created Managed System Id | success | int | 123 |
| name | Created Managed System Name | success | str | Managed System Name |
Lookup Plugins
Lookup Plugin: functional_accounts_list
Short Description
Retrieve functional accounts list from Password Safe.
Description
Custom lookup plugin to fetch functional accounts list from Password Safe.
Parameters
| Name | Description | Type | Required | Default |
|---|---|---|---|---|
| api_url | BeyondTrust Password Safe API URL. | str | ✅ Yes | |
| api_version | The recommended version is 3.1. If no version is specified, the default API version 3.0 will be used. | str | ❌ No | 3.0 |
| client_id | API OAuth Client ID | str | ✅ Yes | |
| client_secret | API OAuth Client Secret. | str | ✅ Yes | |
| log_level | Log file's log level (INFO, DEBUG, WARNING, ERROR). | str | ❌ No | DEBUG |
| log_file_name | Log file's name | str | ❌ No | ansible-collection-modules-logs |
| verify_ca | Verify CA parameter for SSL certificate validation. If set to False, SSL certificate validation will be disabled, which is insecure and exposes you to man-in-the-middle attacks. Only set to False for testing purposes in trusted environments. | bool | ❌ No | True |
Example--- - vars: # PASSWORD_SAFE_API_URL, PASSWORD_SAFE_CLIENT_ID and PASSWORD_SAFE_CLIENT_SECRET are environment variables. api_url: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_API_URL') }}" client_id: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_CLIENT_ID') }}" client_secret: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_CLIENT_SECRET') }}" functional_accounts: >- {{ lookup('beyondtrust.password_safe.functional_accounts_list', api_url=api_url, client_id=client_id, client_secret=client_secret) }} tasks: - name: Print functional accounts list debug: msg: "{{ functional_accounts }}" - name: Print test Functional account debug: msg: "{{ functional_accounts | selectattr('AccountName', 'equalto', 'test') | first }}"
Return values
| Name | Description | Returned | Type | Sample |
|---|---|---|---|---|
| _list | list of all functional accounts. | list |
Lookup Plugin: workgroups_list
Short Description
Retrieve workgroups list from Password Safe.
Description
Custom lookup plugin to fetch workgroups list from Password Safe.
Parameters
| Name | Description | Type | Required | Default |
|---|---|---|---|---|
| api_url | BeyondTrust Password Safe API URL. | str | ✅ Yes | |
| api_version | The recommended version is 3.1. If no version is specified, the default API version 3.0 will be used. | str | ❌ No | 3.0 |
| client_id | API OAuth Client ID | str | ✅ Yes | |
| client_secret | API OAuth Client Secret. | str | ✅ Yes | |
| log_level | Log file's log level (INFO, DEBUG, WARNING, ERROR). | str | ❌ No | DEBUG |
| log_file_name | Log file's name | str | ❌ No | ansible-collection-modules-logs |
| verify_ca | Verify CA parameter for SSL certificate validation. If set to False, SSL certificate validation will be disabled, which is insecure and exposes you to man-in-the-middle attacks. Only set to False for testing purposes in trusted environments. | bool | ❌ No | True |
| workgroup_id | The Workgroup ID, if want to search by Workgroup ID. | N/A | ❌ No | |
| workgroup_name | The Workgroup name, if want to search by Workgroup name. | N/A | ❌ No |
Example--- - vars: # PASSWORD_SAFE_API_URL, PASSWORD_SAFE_CLIENT_ID and PASSWORD_SAFE_CLIENT_SECRET are environment variables. api_url: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_API_URL') }}" client_id: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_CLIENT_ID') }}" client_secret: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_CLIENT_SECRET') }}" workgroups: "{{ lookup('beyondtrust.password_safe.workgroups_list', api_url=api_url, client_id=client_id, client_secret=client_secret) }}" tasks: - name: Print Workgroups list debug: msg: "{{ workgroups }}" - name: Default Workgroup debug: msg: "{{ workgroups | selectattr('Name', 'equalto', 'Default Workgroup') | first }}"
Return values
| Name | Description | Returned | Type | Sample |
|---|---|---|---|---|
| _list | list of all workgroups. | list |
Lookup Plugin: assets_list
Short Description
Retrieve assets list from Password Safe.
Description
Custom lookup plugin to fetch assets list from Password Safe.
Parameters
| Name | Description | Type | Required | Default |
|---|---|---|---|---|
| api_url | BeyondTrust Password Safe API URL. | str | ✅ Yes | |
| api_version | The recommended version is 3.1. If no version is specified, the default API version 3.0 will be used. | str | ❌ No | 3.0 |
| client_id | API OAuth Client ID | str | ✅ Yes | |
| client_secret | API OAuth Client Secret. | str | ✅ Yes | |
| log_level | Log file's log level (INFO, DEBUG, WARNING, ERROR). | str | ❌ No | DEBUG |
| log_file_name | Log file's name | str | ❌ No | ansible-collection-modules-logs |
| verify_ca | Verify CA parameter for SSL certificate validation. If set to False, SSL certificate validation will be disabled, which is insecure and exposes you to man-in-the-middle attacks. Only set to False for testing purposes in trusted environments. | bool | ❌ No | True |
| workgroup_id | The Workgroup ID, if want to search by Workgroup ID. | N/A | ❌ No | |
| workgroup_name | The Workgroup name, if want to search by Workgroup name. | N/A | ❌ No |
Example--- - vars: # PASSWORD_SAFE_API_URL, PASSWORD_SAFE_CLIENT_ID and PASSWORD_SAFE_CLIENT_SECRET are environment variables. api_url: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_API_URL') }}" client_id: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_CLIENT_ID') }}" client_secret: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_CLIENT_SECRET') }}" assets: "{{ lookup('beyondtrust.password_safe.assets_list', api_url=api_url, client_id=client_id, client_secret=client_secret) }}" tasks: - name: Print Assets list debug: msg: "{{ assets }}" - name: Print MyNewAsset2 Asset debug: msg: "{{ assets | selectattr('AssetName', 'equalto', 'MyNewAsset2') | first }}"
Return values
| Name | Description | Returned | Type | Sample |
|---|---|---|---|---|
| _list | list of all assets. | list |
Lookup Plugin: managed_accounts_list
Short Description
Retrieve managed accounts list from Password Safe.
Description
Custom lookup plugin to fetch managed accounts list from Password Safe.
Parameters
| Name | Description | Type | Required | Default |
|---|---|---|---|---|
| api_url | BeyondTrust Password Safe API URL. | str | ✅ Yes | |
| api_version | The recommended version is 3.1. If no version is specified, the default API version 3.0 will be used. | str | ❌ No | 3.0 |
| client_id | API OAuth Client ID | str | ✅ Yes | |
| client_secret | API OAuth Client Secret. | str | ✅ Yes | |
| log_level | Log file's log level (INFO, DEBUG, WARNING, ERROR). | str | ❌ No | DEBUG |
| log_file_name | Log file's name | str | ❌ No | ansible-collection-modules-logs |
| verify_ca | Verify CA parameter for SSL certificate validation. If set to False, SSL certificate validation will be disabled, which is insecure and exposes you to man-in-the-middle attacks. Only set to False for testing purposes in trusted environments. | bool | ❌ No | True |
| workgroup_id | The Workgroup ID, if want to search by Workgroup ID. | N/A | ❌ No | |
| workgroup_name | The Workgroup name, if want to search by Workgroup name. | N/A | ❌ No |
Example--- - vars: # PASSWORD_SAFE_API_URL, PASSWORD_SAFE_CLIENT_ID and PASSWORD_SAFE_CLIENT_SECRET are environment variables. api_url: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_API_URL') }}" client_id: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_CLIENT_ID') }}" client_secret: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_CLIENT_SECRET') }}" managed_accounts: "{{ lookup('beyondtrust.password_safe.managed_accounts_list', api_url=api_url, client_id=client_id, client_secret=client_secret) }}" tasks: - name: Print Managed Accounts list debug: msg: "{{ managed_accounts }}" - name: Print managed_account01 Managed Account debug: msg: "{{ managed_accounts | selectattr('AccountDescription', 'equalto', 'managed_account01') | first }}"
Return values
| Name | Description | Returned | Type | Sample |
|---|---|---|---|---|
| _list | list of all managed accounts. | list |
Lookup Plugin: platforms_list
Short Description
Retrieve platforms list from Password Safe.
Description
Custom lookup plugin to fetch platforms list from Password Safe.
Parameters
| Name | Description | Type | Required | Default |
|---|---|---|---|---|
| api_url | BeyondTrust Password Safe API URL. | str | ✅ Yes | |
| api_version | The recommended version is 3.1. If no version is specified, the default API version 3.0 will be used. | str | ❌ No | 3.0 |
| client_id | API OAuth Client ID | str | ✅ Yes | |
| client_secret | API OAuth Client Secret. | str | ✅ Yes | |
| log_level | Log file's log level (INFO, DEBUG, WARNING, ERROR). | str | ❌ No | DEBUG |
| log_file_name | Log file's name | str | ❌ No | ansible-collection-modules-logs |
| verify_ca | Verify CA parameter for SSL certificate validation. If set to False, SSL certificate validation will be disabled, which is insecure and exposes you to man-in-the-middle attacks. Only set to False for testing purposes in trusted environments. | bool | ❌ No | True |
| workgroup_id | The Workgroup ID, if want to search by Workgroup ID. | N/A | ❌ No | |
| workgroup_name | The Workgroup name, if want to search by Workgroup name. | N/A | ❌ No |
Example--- - vars: # PASSWORD_SAFE_API_URL, PASSWORD_SAFE_CLIENT_ID and PASSWORD_SAFE_CLIENT_SECRET are environment variables. api_url: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_API_URL') }}" client_id: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_CLIENT_ID') }}" client_secret: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_CLIENT_SECRET') }}" platforms: "{{ lookup('beyondtrust.password_safe.folders_list', api_url=api_url, client_id=client_id, client_secret=client_secret) }}" tasks: - name: Print Platforms list debug: msg: "{{ platforms }}" - name: Print XING Platform debug: msg: "{{ platforms | selectattr('Name', 'equalto', 'XING') | first }}"
Return values
| Name | Description | Returned | Type | Sample |
|---|---|---|---|---|
| _list | list of all platforms. | list |
Lookup Plugin: managed_systems_list
Short Description
Retrieve managed systems list from Password Safe.
Description
Custom lookup plugin to fetch managed systems list from Password Safe.
Parameters
| Name | Description | Type | Required | Default |
|---|---|---|---|---|
| api_url | BeyondTrust Password Safe API URL. | str | ✅ Yes | |
| api_version | The recommended version is 3.1. If no version is specified, the default API version 3.0 will be used. | str | ❌ No | 3.0 |
| client_id | API OAuth Client ID | str | ✅ Yes | |
| client_secret | API OAuth Client Secret. | str | ✅ Yes | |
| log_level | Log file's log level (INFO, DEBUG, WARNING, ERROR). | str | ❌ No | DEBUG |
| log_file_name | Log file's name | str | ❌ No | ansible-collection-modules-logs |
| verify_ca | Verify CA parameter for SSL certificate validation. If set to False, SSL certificate validation will be disabled, which is insecure and exposes you to man-in-the-middle attacks. Only set to False for testing purposes in trusted environments. | bool | ❌ No | True |
| workgroup_id | The Workgroup ID, if want to search by Workgroup ID. | N/A | ❌ No | |
| workgroup_name | The Workgroup name, if want to search by Workgroup name. | N/A | ❌ No |
Example--- - vars: # PASSWORD_SAFE_API_URL, PASSWORD_SAFE_CLIENT_ID and PASSWORD_SAFE_CLIENT_SECRET are environment variables. api_url: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_API_URL') }}" client_id: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_CLIENT_ID') }}" client_secret: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_CLIENT_SECRET') }}" managed_systems: "{{ lookup('beyondtrust.password_safe.managed_systems_list', api_url=api_url, client_id=client_id, client_secret=client_secret) }}" tasks: - name: Print Managed Systems list debug: msg: "{{ managed_systems }}" - name: Print system01 Managed System debug: msg: "{{ managed_systems | selectattr('SystemName', 'equalto', 'system01') | first }}"
Return values
| Name | Description | Returned | Type | Sample |
|---|---|---|---|---|
| _list | list of all managed systems. | list |
Lookup Plugin: databases_list
Short Description
Retrieve databases list from Password Safe.
Description
Custom lookup plugin to fetch databases list from Password Safe.
Parameters
| Name | Description | Type | Required | Default |
|---|---|---|---|---|
| api_url | BeyondTrust Password Safe API URL. | str | ✅ Yes | |
| api_version | The recommended version is 3.1. If no version is specified, the default API version 3.0 will be used. | str | ❌ No | 3.0 |
| client_id | API OAuth Client ID | str | ✅ Yes | |
| client_secret | API OAuth Client Secret. | str | ✅ Yes | |
| log_level | Log file's log level (INFO, DEBUG, WARNING, ERROR). | str | ❌ No | DEBUG |
| log_file_name | Log file's name | str | ❌ No | ansible-collection-modules-logs |
| verify_ca | Verify CA parameter for SSL certificate validation. If set to False, SSL certificate validation will be disabled, which is insecure and exposes you to man-in-the-middle attacks. Only set to False for testing purposes in trusted environments. | bool | ❌ No | True |
Example--- - vars: # PASSWORD_SAFE_API_URL, PASSWORD_SAFE_CLIENT_ID and PASSWORD_SAFE_CLIENT_SECRET are environment variables. api_url: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_API_URL') }}" client_id: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_CLIENT_ID') }}" client_secret: "{{ lookup('ansible.builtin.env', 'PASSWORD_SAFE_CLIENT_SECRET') }}" databases: "{{ lookup('beyondtrust.password_safe.databases_list', api_url=api_url, client_id=client_id, client_secret=client_secret) }}" tasks: - name: Print databases list debug: msg: "{{ databases }}" - name: Print test database debug: msg: "{{ databases | selectattr('InstanceName', 'equalto', 'test') | first }}"
Return values
| Name | Description | Returned | Type | Sample |
|---|---|---|---|---|
| _list | list of all databases. | list |
Updated 15 days ago

