Welcome to Identity Security Insights | Insights
Identity Security Insights helps you understand and act on identity risk — fast.
It maps how access works — and how it can escalate — so you can detect threats, reduce privilege, and improve posture across hybrid environments.
Built to fit into your existing identity stack, Insights gives you real-time visibility and contextual recommendations without requiring a reset.
What it does
Identity Security Insights gives security teams a dynamic view of how identities operate across systems, roles, and entitlements.
At the core is the True Privilege Graph — a map that shows:
- What users can access (directly and indirectly)
- How access can evolve through vertical and lateral movement
The graph reveals hidden access paths that traditional role reviews often miss.
Why it matters
Identities are often the most targeted — and least understood — part of your attack surface.
Insights helps you move beyond static access reviews into real-time identity intelligence, so you can:
- Uncover escalation paths
- Reduce blast radius
- Track posture improvements
- Detect active identity threats
Key capabilities
- True Privilege™: See what identities can do, not just what they’re assigned
- Posture Tracking: Measure privilege reduction, MFA adoption, and dormant account cleanup
- Threat Detection: Spot session hijacking, unauthorized changes, and misuse of service principals
- Prebuilt Reports: Cover hygiene, misuse, and behavioral anomalies
- Cross-Domain Correlation: Surface hidden relationships across cloud and on-premises environments
- Contextual Recommendations: Know what to do next, with insights tied to each detection
Reports are continuously updated to reflect new identity risk patterns.
How It Works
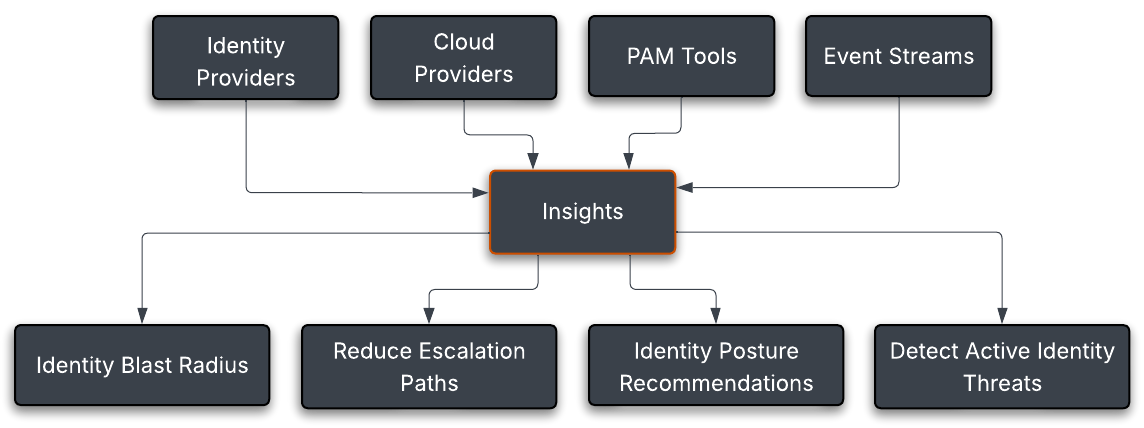
Insights correlates and analyzes data from many sources – identity providers, PAM tools, SaaS platforms, and cloud environments to show who can do what, where - and whether they should.
- Connect identity sources (AD, Entra ID, Okta, AWS, BeyondTrust tools, and more!)
- Ingest and normalize identity data
- Visualize access and escalation paths
- Detect risky behavior
- Take action via integrations with your existing security stack
This flow gives you a full picture of identity risk — from visibility to action.
System requirements
Identity Security Insights supports the following browsers:
- Microsoft Edge
- Google Chrome
- Apple Safari
- Opera
Updated 5 months ago
