Entitle December 2025 release notes
✨Enhancements
AWS integration: Improved visibility into SSO group-based access
The AWS integration now maps indirect access paths from users to AWS accounts via SSO groups and permission sets. Entitle captures user–group membership and both direct and group-based permission set assignments, providing a complete view of who can access which AWS accounts and through which permission sets. This supports more accurate access reviews and stronger governance.
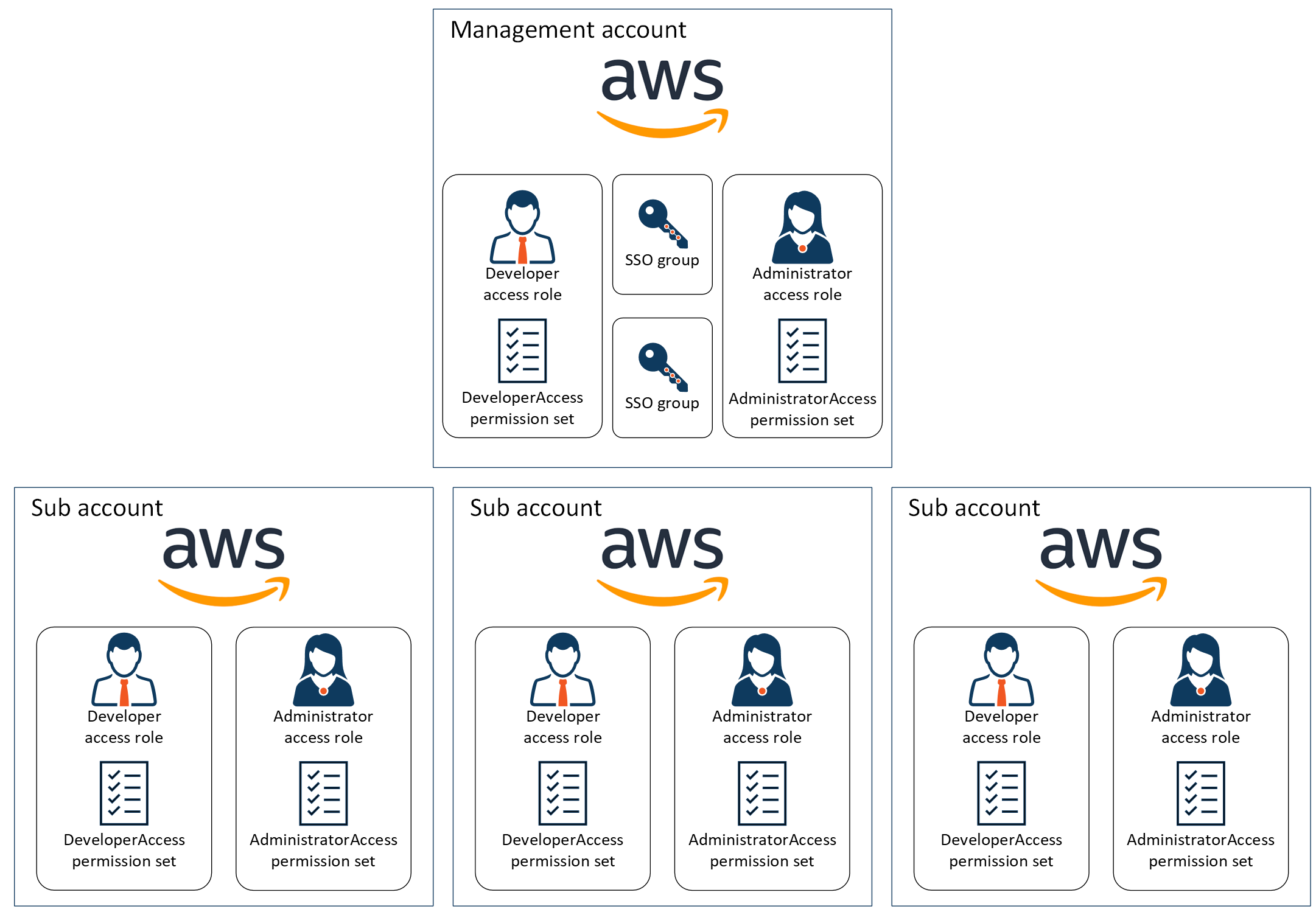
For more information, see AWS Identity Center - basic integration.
Azure integration: Surface indirect group-based permissions
The Azure integration now fully reflects permissions granted indirectly through Azure AD group membership. Entitle exposes all supported asset-to-asset permission paths, providing a complete view of effective access when roles are assigned via groups. These paths have been validated end to end to ensure accuracy and consistency in access visibility.
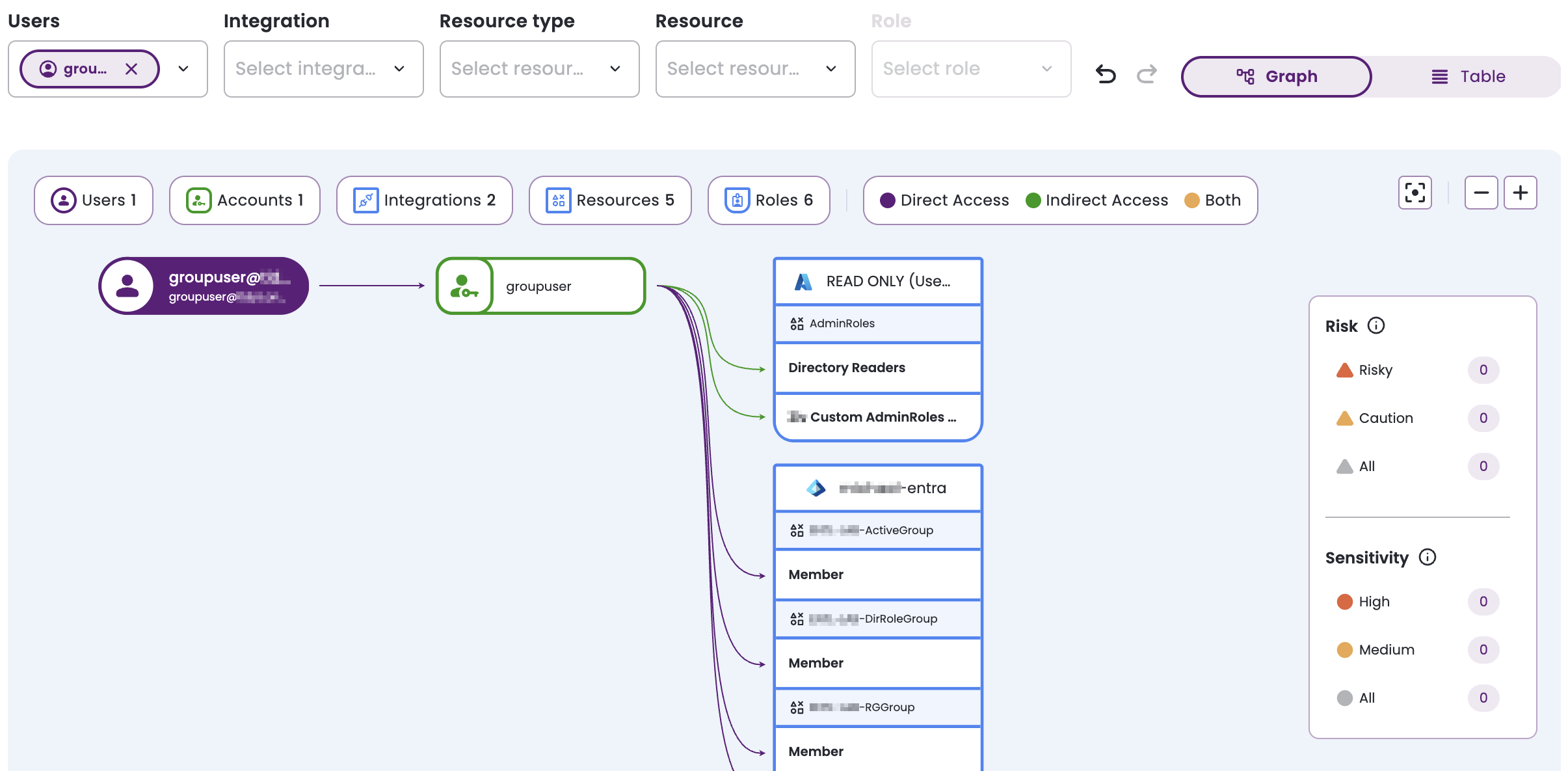
For more information, see The permissions graph.
Azure DevOps integration: Support multiple roles per repository
The Azure DevOps integration now supports assigning multiple roles to the same account for repository resources. This allows Entitle to accurately reflect effective permissions when users or groups hold more than one role on a repository, aligning Entitle access visibility with Azure DevOps permission behavior.
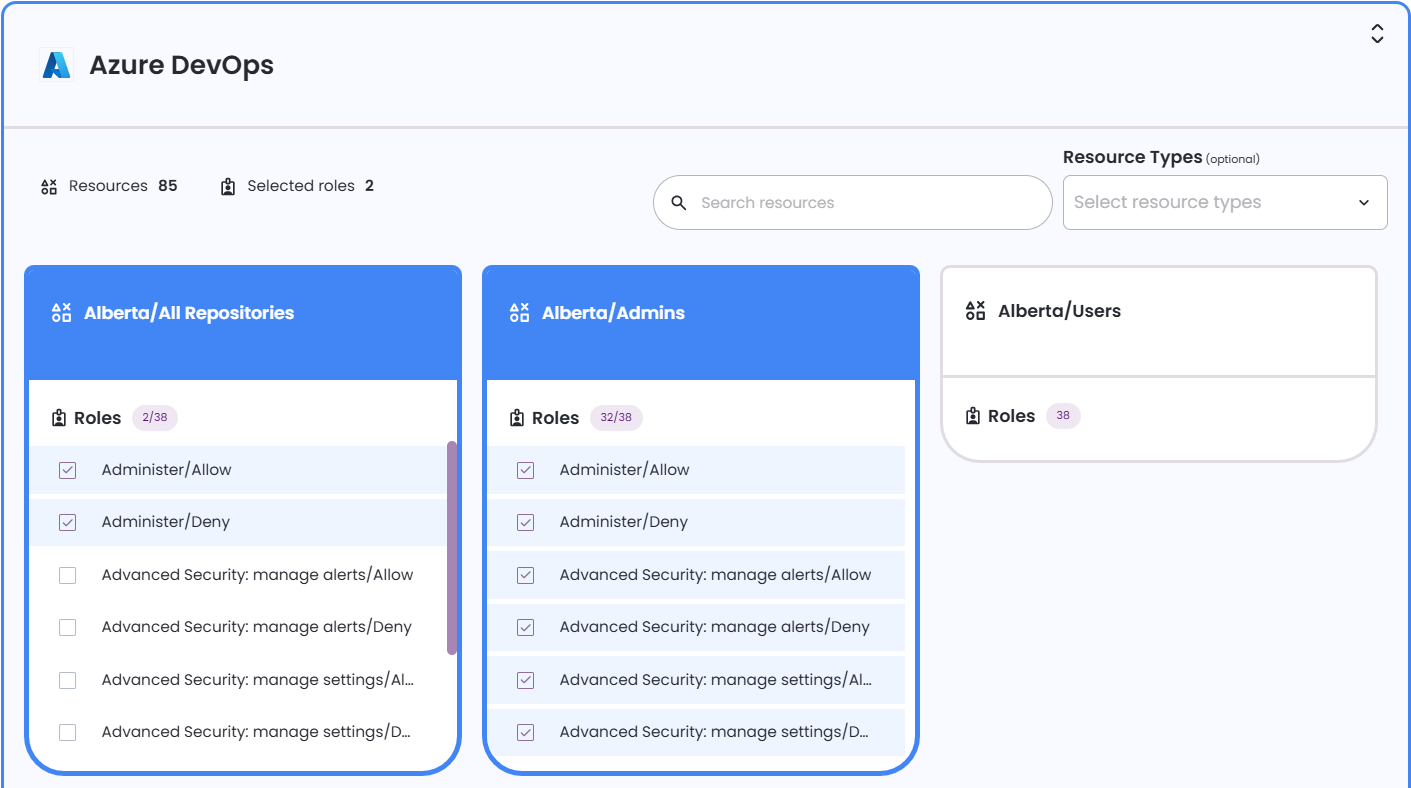
For more information, see Create a new request.
Azure Workload Identity: Support federated credentials for Teams integration
The Teams integration now supports Azure Workload Identity using federated credentials for upgraded agents. You can configure the integration to authenticate with federated credentials instead of client secrets, reducing secret management overhead while maintaining secure access.
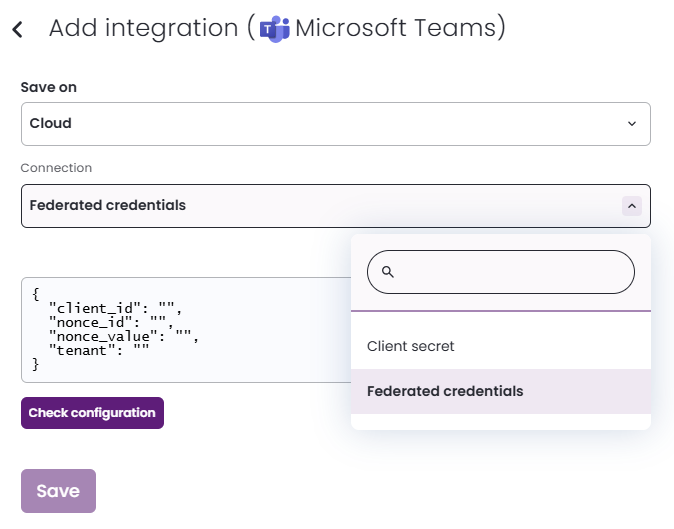
For more information, see Set up Microsoft Teams to work with Entitle.
Email notifications: Notification options are now generally available
The email notification setting is now configurable for all customers without requiring enablement by Support. From the Org settings page, admins can enable email notifications for request activity, permission changes, upcoming expirations, and comments. Previously, this option was hidden behind a feature flag and available only on request.
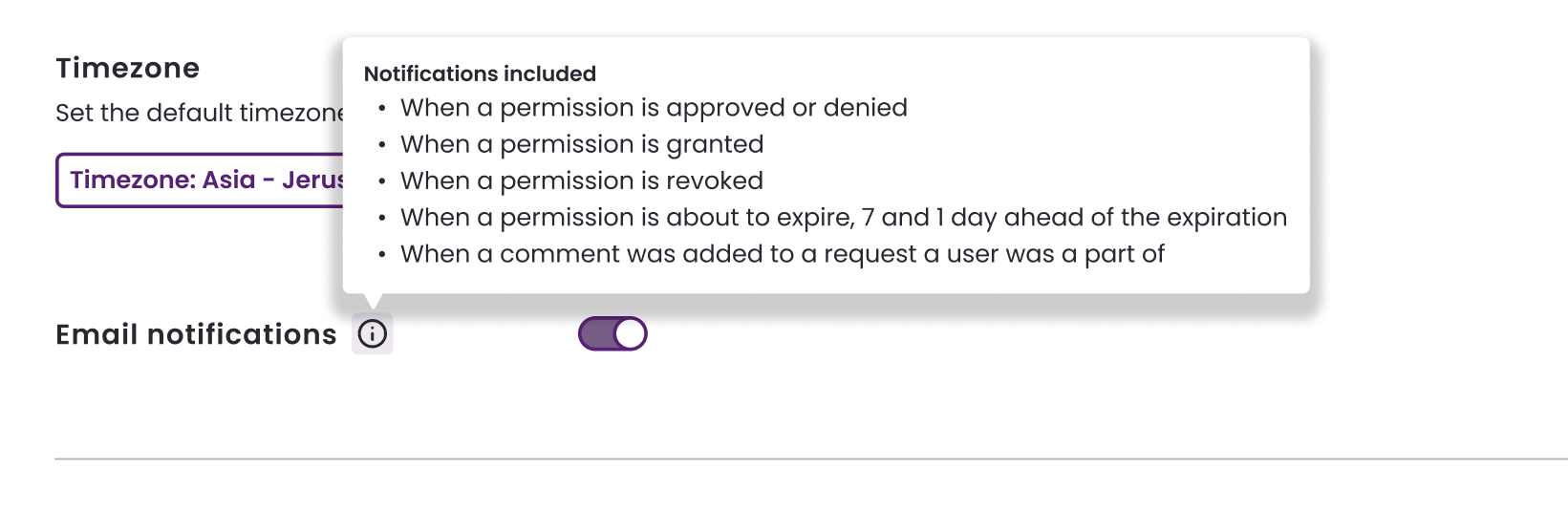
For more information, see Enable email notifications.
Google Cloud Platform integration: Support ephemeral accounts using workload-based identity
The Google Cloud Platform access and directory adapters now support authentication using workload-based identity through Google Workload Identity Federation. This enables Entitle to authenticate to GCP without long-lived service account keys, using ephemeral credentials that integrate with cloud-native identity federation. The integration supports Entitle cloud agents and aligns with modern OIDC-based authentication practices.
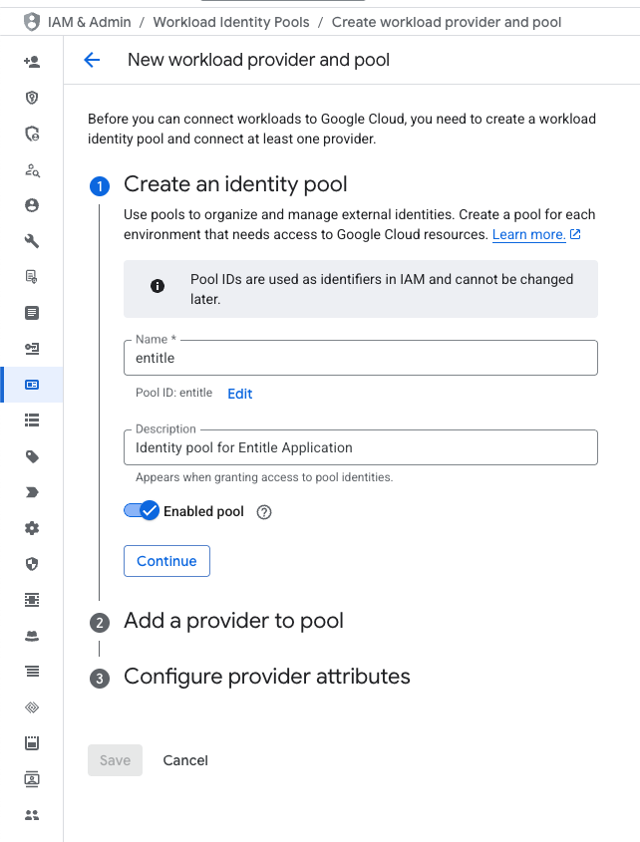
For more information, see Service account key vs. Workload Identity Federation.
JIT request analysis: Analyze and export JIT access eligibility
Admins and compliance teams can now analyze JIT access eligibility across users, roles, and resources. The JIT access analysis provides a detailed view of which users can request specific roles and resources, with filtering to support audit, investigation, and governance needs. Export reports to CSV, with direct links to related roles, bundles, and virtual applications to support fast remediation when issues are identified.
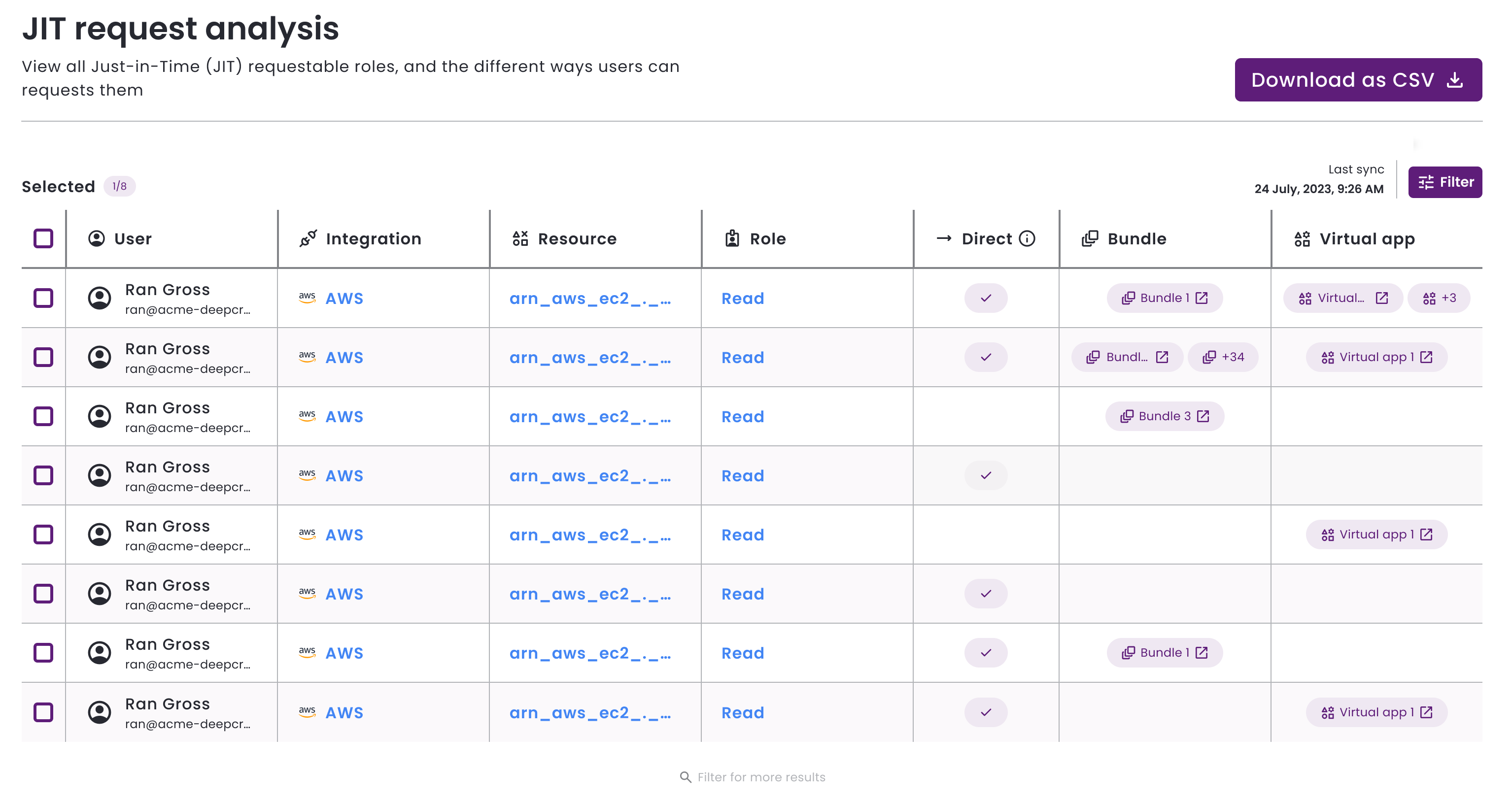
For more information, see View JIT request analysis.
Microsoft Active Directory IdP connection: Support self-signed certificate configuration
The Microsoft Active Directory IdP connection now supports configuring self-signed certificates directly from the web portal. Admins can provide a self-signed certificate to enable SSL. This allows secure connectivity in environments that do not rely on certificates issued by a public certificate authority.
Additionally, the IdP connection automatically determines the appropriate certificate validation behavior at runtime. This removes the need for manual configuration or additional settings, ensuring compatibility across on-premises environments.
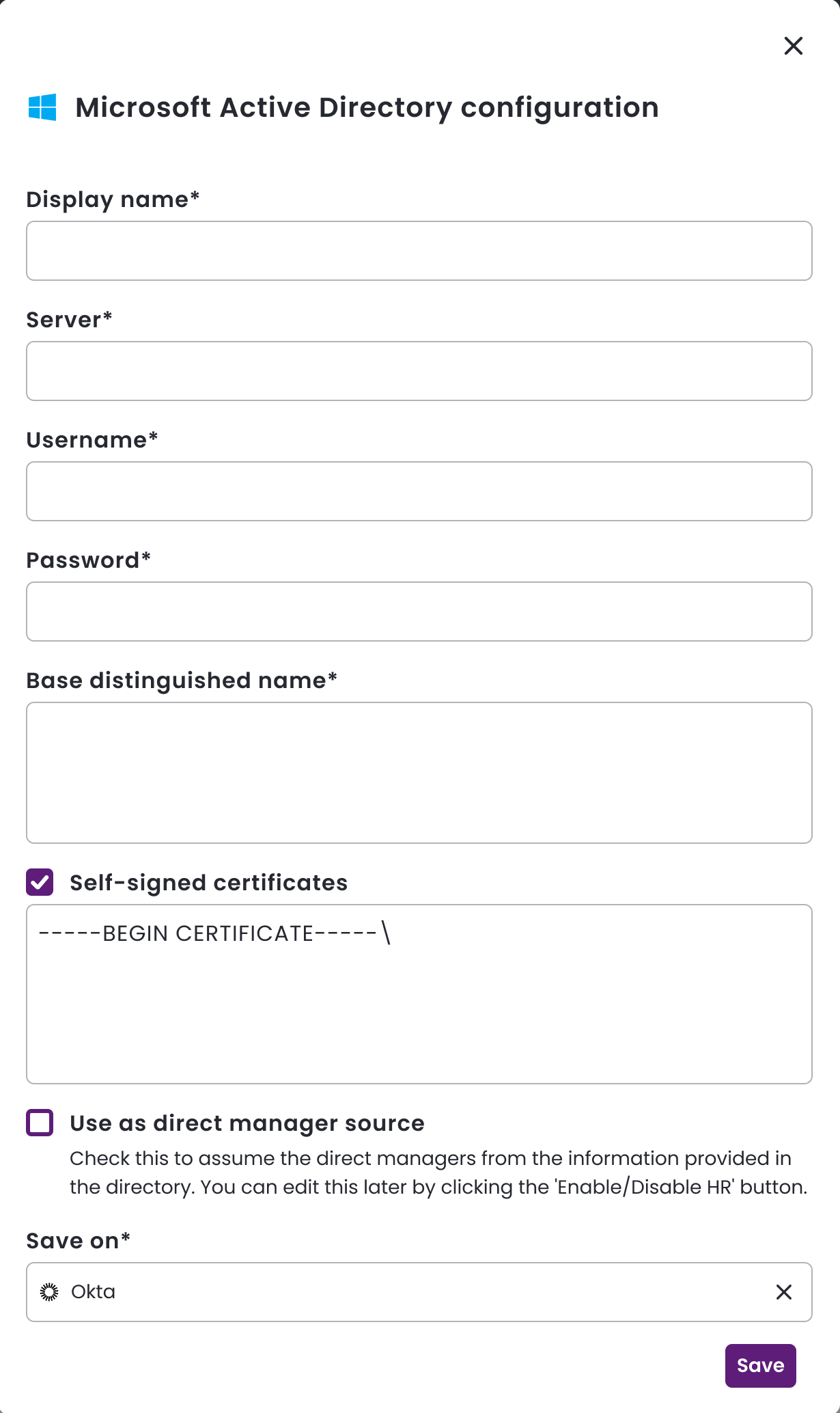
For more information, see Active Directory: Create the integration in Entitle and Active Directory IdP connection: Connecting your IdP in Entitle.
Microsoft SQL adapter: Support least-privilege connector login
The Microsoft SQL adapter now supports running with a non-sysadmin SQL Server login, reducing the need to grant full sysadmin privileges to the connector account. When the connector does not have sysadmin privileges, it validates that the login has the required server-level and database-level permissions, providing clear, actionable error messages if required permissions are missing.
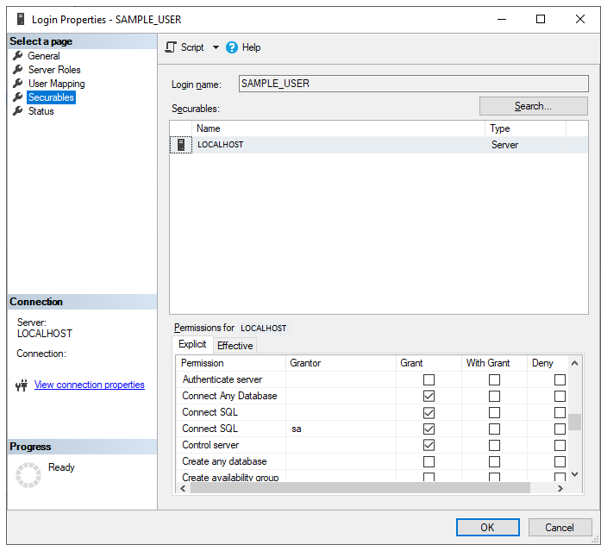
For more information, see Microsoft SQL Server: Least-privilege operating mode.
Token management: Improve creation, visibility, and revocation experience
Token management has been streamlined to reduce clicks and improve usability across API, agent and personal access tokens. Admins can now create, name, and manage tokens directly from a consolidated table view on the Org settings page, with clearer validation, safer token reveal behavior, and simplified revocation flows. These improvements make it easier to manage tokens securely and efficiently throughout their lifecycle.
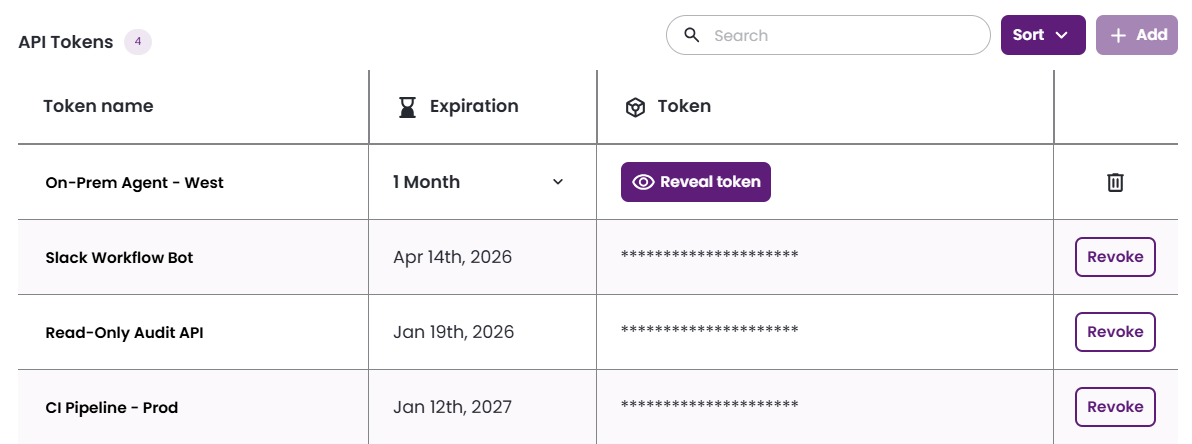
For more information, see Tokens.
📝Documentation
AWS pod-based integrations: US-specific setup instructions
AWS pod-based integration guides have been updated to include US-based Entitle environments. The AWS Identity Center and IAM pod-based guides now document the required setup for US tenants, ensuring consistent guidance across regions.
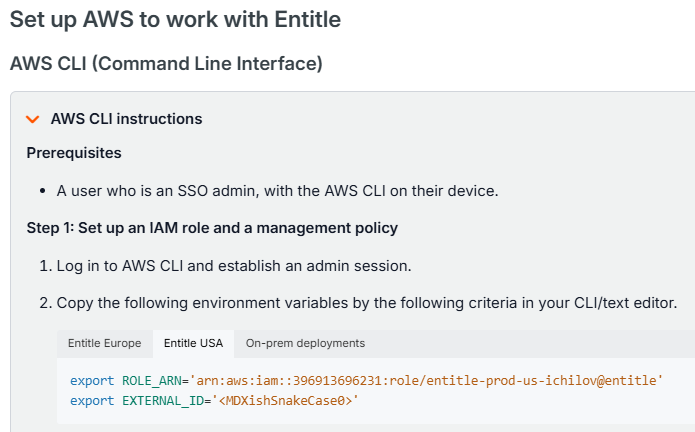
For more information, see:
