Users & security | PRA Pathfinder
What is the Users page?
The Users page allows administrators to manage individual user accounts, including creating, editing, and deleting accounts. It provides detailed control over user-specific settings, permissions, and roles within the Privileged Remote Access environment.
How is the Users page useful to my organization?
The Users page enables administrators to customize access and permissions for each user, ensuring security and proper role alignment. It also allows for efficient user management, helping to maintain compliance and support operational needs.
How do I access the Users page?
- Sign into app.beyondtrust.io.
The BeyondTrust Home page displays. - From the main menu, click Privileged Remote Access > Users & Security.
The User & Security page opens and the Users tab displays by default.
The Users page
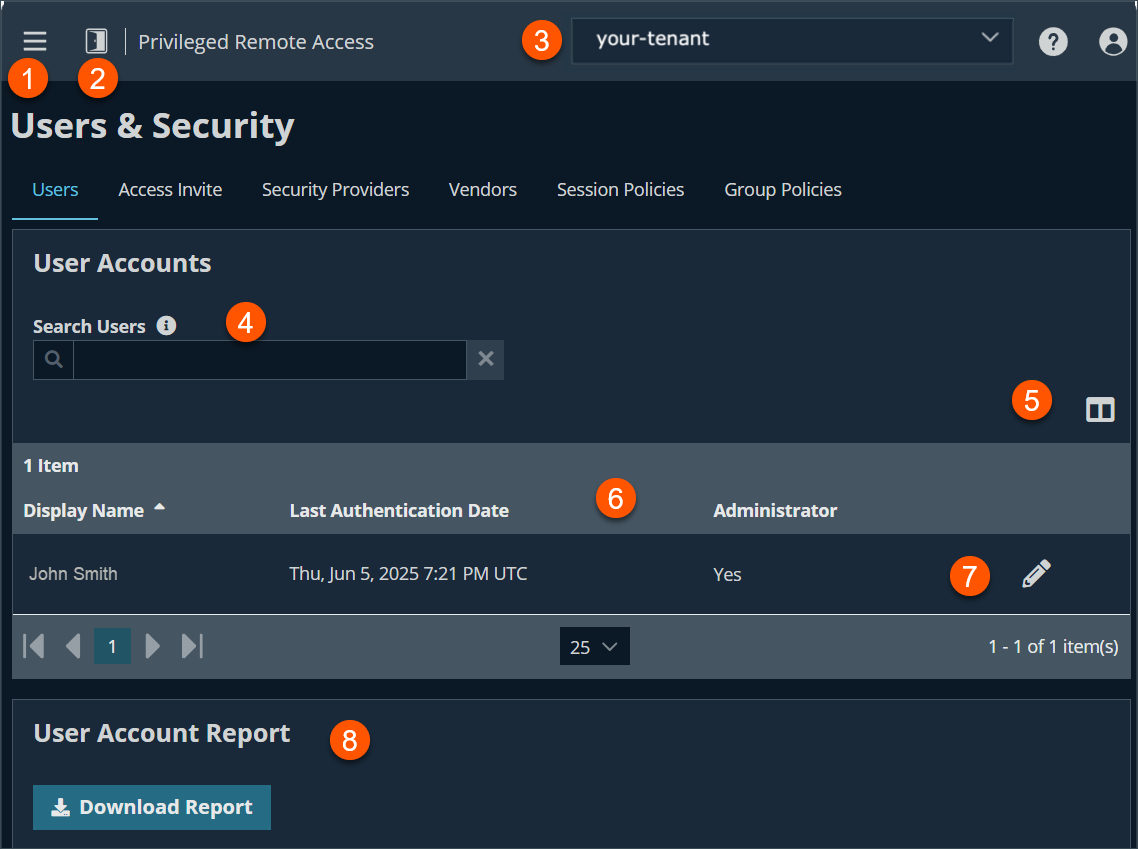
-
Filter: Search users based on Last Authenticated As, Display Name or Email Address.
-
Hide columns: Option to hide/display columns.
-
Users columns: The list of Users columns. Not all of the columns are displayed.
Users columns
- Last Authenticated As: The name of the user in the form of [email protected].
- Display Name: The full name of the account. For example, "John Smith".
- Last Authentication Date: The last date the user logged on.
- Administrator: Defines whether the user is an administrator which is defined in General Permission section of the Users & Security > Group Policies page. The value of the column is Yes or No.
-
Users list options: Edit or delete a user.
-
Download Report: Generate a report for user accounts.
User accounts
This page is changed in Pathfinder. You can still search for users, edit the users, and obtain a user account report on the Users page. However, the ability to add new users and synchronize the users and groups associated with an external security provider is removed. There is now a single point of user management for all products hosted on Pathfinder. This is performed on the User Management page.
How to add, edit, or delete a user from Pathfinder
How to manage users
- Sign into app.beyondtrust.io.
The BeyondTrust Home page displays. - Sign into the Administration tenant located in the upper-right hand corner with administrative permission.
- Click the hamburger menu
 in the upper left-hand corner of the window.
in the upper left-hand corner of the window. - In the User Administration section, click User Management.
The Organization Users page displays.
Add a new user
- Click Invite User.
- In User Details section, enter an Email Address, First Name, and Last Name. All fields are required.
- In the User Permissions section, for Organization Role, select either Standard User or Administrator.
- For Site Access, select the site(s) and at least one application you wish to grant user access to.
- Click Invite User.
Edit a user
- From the list of users, click the ellipsis
 .
. - Click Edit User.
- Make the necessary changes, and then click Save Changes.
Delete a user
- From the list of users, click the ellipsis
 .
. - Click Delete User.
How to manage users in Privileged Remote Access
Search users
Search for a specific user account based on username, display name, or email address.
User account report
At the bottom of the page, export detailed information about your users for auditing purposes. Gather detailed information for all users, users from a specific security provider, or just local users. Information collected includes group policy and team memberships and permissions.
User settings
Memberships
Account settings
General permissions
Access permissions
- Allowed to access endpoints: Enables the user to use the access console in order to run sessions. If endpoint access is enabled, options pertaining to endpoint access will also be available.
- Session management
- Allowed to share sessions with teams which they do not belong to: Enables the user to invite a less limited set of user to share sessions, not only their team members. Combined with the extended availability permission, this permission expands session sharing capabilities.
- Allowed to invite external users: Enables the user to invite third-party users to participate in a session, one time only.
- Remove User from session after inactivity: Sets the time interval to remove a user from a session after inactivity. Values range from No Timeout to 24 hours.
- Allowed to enable extended availability mode: Enables the user to receive email invitations from other users requesting to share a session even when they are not logged into the access console.
- Allowed to edit the external key: Enables the user to modify the external key from the session info pane of a session within the access console.
- User to user screen sharing
- Allowed to show screen to other users: Enables the user to share their screen with another user without the receiving user having to join a session. This option is available even if the user is not in a session.
- Allowed to give control when showing screen to other users: Enables the user sharing their screen to give keyboard and mouse control to the user viewing their screen.
- Jump Technology
- Allowed Jump Item methods: Enables the user to Jump to computers using the following:
- Jump Clients
- Local Jump (Windows only)
- Remote Jump
- Remove VNC
- Web Jump
- Remote RDP
- Shell Jump
- Protocol Tunnel Jump
- Jump Item Roles: A Jump Item Role is a predefined set of permissions regarding Jump Item management and usage. For each option, click Show to open the Jump Item Role in a new tab.
- The Default role is used only when Use User's Default is set for that user in a Jump Group.
- The Personal role applies only to Jump Items pinned to the user's personal list of Jump Items.
- The Teams role applies to Jump Items pinned to the personal list of Jump Items of a team member of a lower role. For example, a team manager can view team leads' and team members' personal Jump Items, and a team lead can view team members' personal Jump Items.
- The System role applies to all other Jump Items in the system. For most users, this should be set to No Access. If set to any other option, the user is added to Jump Groups to which they would not normally be assigned, and in the access console, they can see non-team members' personal lists of Jump Items.
- The Endpoint automation role sets how a user can use endpoint automation.
- Not allowed prevents them from seeing the Jump > Endpoint Automation tab altogether.
- A User can create new automation jobs with these restrictions:
- They are able to choose any existing Script Template but cannot edit the Script Template, Script Command, nor select or change the template accompanying Resources.
- The Script Template, Script Command, Operating System, and Resources fields are unavailable.
- They can run scripts only on Jump Items where their Jump Item Role includes the Start Sessions permission (set on the Jump > Jump Items Role page).
- An Administrator has full access and ability to create Jobs, Scripts Templates, and Resources.
For more information, see Jump Item Roles and Endpoint Automation.
- External tools
- Enable static port and username for external tool sessions: This option accepts two values:
- Enable: Ensures that the port and username generated for a user starting a session with a Jump item using external tools are preserved from session to session.
- Disable: A new port number and username are randomly generated for that user every time they start a new session with each Jump item.
- Enable static port and username for external tool sessions: This option accepts two values:
- Allowed Jump Item methods: Enables the user to Jump to computers using the following:
Session permissions
Availability settings
Updated 5 months ago
