Identity Security Insights 26.03.1
🆕 New features
A Fresh Look for Detections & Recommendations
The Detections and Recommendations pages now match the modern look and feel you're used to across Accounts, Identities, and Entitlements. Both grouped and ungrouped views have been updated with cleaner visuals and a more consistent layout, making it easier to scan and triage findings with the same flow you already use everywhere else.
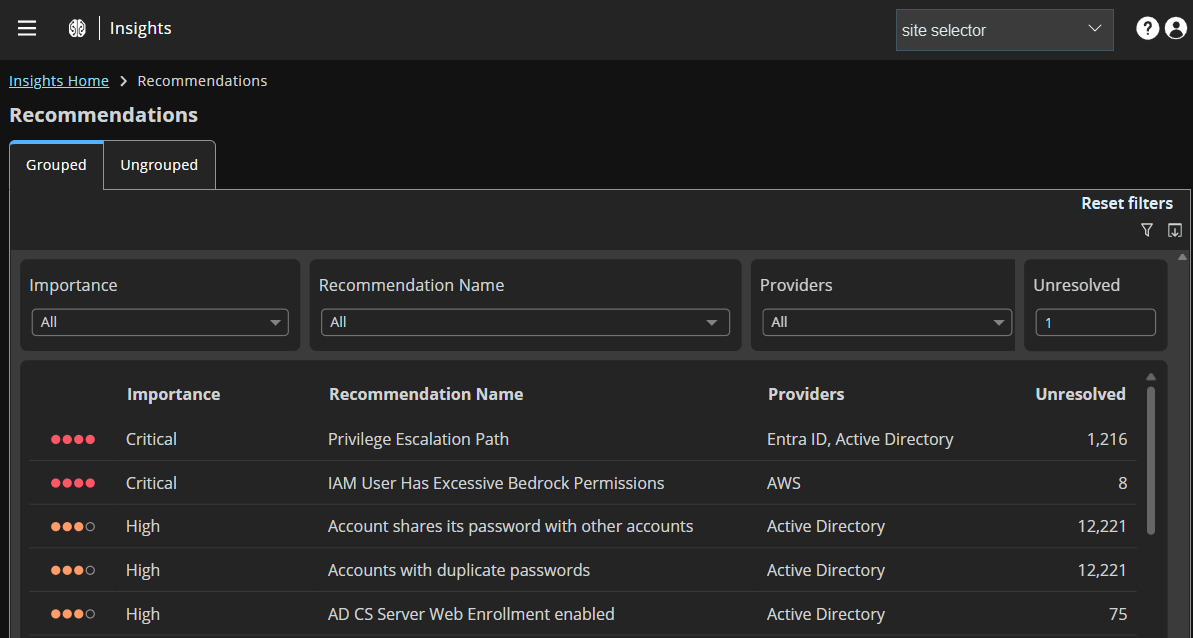
For more information, see Detections and Recommendations.
✨ Enhancements
Bedrock API Key Security
Know Exactly What Your Bedrock API Keys Are Up To
Every time you generate a long-term Bedrock API key, AWS creates a dedicated IAM user and attaches the AmazonBedrockLimitedAccess policy, which is broader than the name suggests. Insights now monitors these users across their lifecycle, flagging unauthorized access keys, tracking bearer token API calls, and surfacing users that have drifted into risky territory.
What you get with this update:
-
Catch unauthorized access keys on Bedrock users
When someone creates a standard IAM access key for one of these auto-provisioned Bedrock users, it gets flagged. These users are only meant for Bedrock API key authentication; a standard AKIA key grants long-term programmatic access to everything the policy allows, including admin-level Bedrock actions. -
Track Bedrock API key calls across your environment
Bedrock API calls made using bearer token authentication are surfaced with context: who made the call, from where, and when. If a key gets leaked or used from an unexpected location, you'll spot it. -
Surface orphaned users that still have broad permissions
When a Bedrock API key is deleted or expires, the IAM user sticks around along with all its permissions. These dormant users are easy to overlook and easy to exploit. They're now flagged so you can clean them up before they become a problem. -
Flag Bedrock users carrying access keys they should never have
Any auto-provisioned Bedrock user that has standard IAM access keys is flagged. These keys expand the attack surface well beyond what Bedrock API keys allow, giving persistent access to any AWS API the policy permits.
For more information, see Amazon Web Services.
AWS Bedrock AI Agents
Control Your Bedrock Data Collection
You can now opt in or opt out of AWS Bedrock data collection directly from the AWS connector creation and settings forms. Existing connectors keep Bedrock data collection enabled by default, and you can update the setting at any time.
